Category: Smartphone » Laptop & Smartphone Theft Recovery
How to Recover Your Lost or Stolen Laptop? Laptop theft is the top 3 computer crimes along with viruses and hacking. On a bigger picture, laptop theft is the second most common crime according to the FBI. What are your odds of being mugged? or encounter a car accident? How do you protect your data and laptop against theft today?
Related Article 😍💰👉 26 Best Android Antivirus – Free Anti-Theft, AppLock, Call Blocker And More
The hardest part when it comes to losing a laptop is when all of your important data is not recoverable or worse, it falls into the wrong hands, thus making you and your company vulnerable to potential lawsuits and loss of profit. If purchasing these services appears to be expensive, try some of the freely available encrypt software, they may not be the best but at least it keeps your data safe for a certain period of time

There are hundreds of software and services that promise you the ability to pinpoint the exact location of your laptop when it is stolen, these services are like insurance and it is costly in the long run. It is crucial to backup your data to a portable hard disk at least every week. Here are some interesting facts on Laptop theft:
- One out of every 10 notebook computers stolen, 90% are not recovered.
- Laptop theft doubled over the past year.
- Over 85% of theft is insider job.
- Laptop theft is one of the top 3 computer crimes along with virus and hacking.
- 81% of U.S. firms lost laptops with sensitive data in the past year.
1. PreyProject
100% free, comes with GPS and SpyCam features
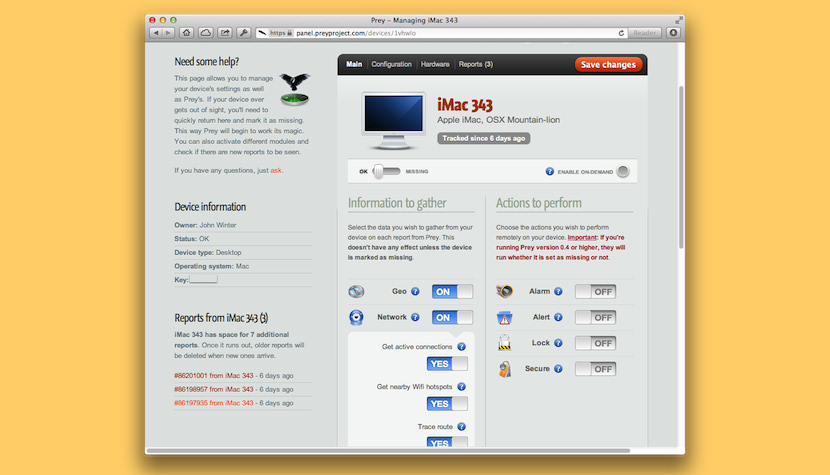
Prey is an anti-theft tracking software for your laptop, phone and tablet that lets you remotely locate, lock, wipe and recover it if ever stolen, or simply missing. You do this by logging into a web platform where you can also trigger actions like sounding an alarm or showing an onscreen message to let the thief know you’re after him. Prey uses a remote activation system which means the program sits silently in your computer until you actually want it to run. If so, it gathers all the information and sends it to your Prey web control panel or directly to your mailbox. Features:
- Wifi auto connect – Prey will attempt to connect to a Wifi to send the necessary information.
- Powerful report system – Will take a screenshot of the desktop or a picture of the thief via the built- in webcam.
- Messaging/alert system – Send a message which will appear on the screen together with a loud alarm to the thief.
- Webcam image capturing – Capture images of the theft silently using the secondary camera.
- Screenshot grabbing – Capture screen shot, this enables you to find out which website he or she is visiting, such as his facebook page.
- Data securing, hardware scanning, screen locking, remote messaging, and sonic-alarm triggering.
2. Hidden Anti Theft
Paid Version, comes with GPS and SpyCam features
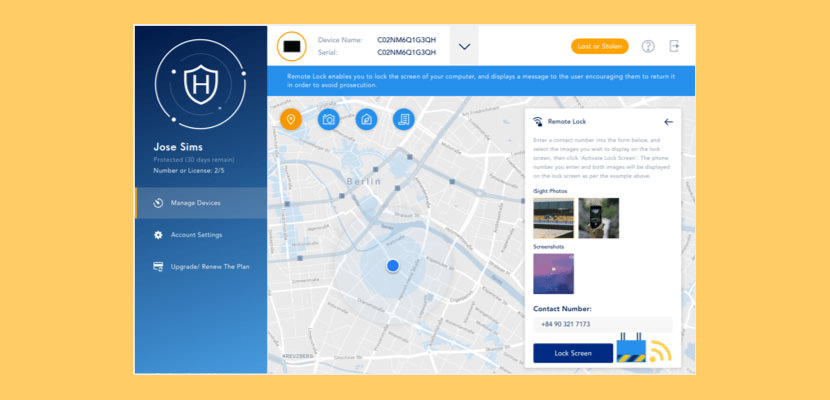
Using proven technology, Hidden tracks your missing Macbook, iPhone or iPad and collects the evidence needed to get them back. And don’t worry. Your personal information stays locked away, too. Get the app that protects your Apple devices, and your privacy.
- Location Tracking – Apple’s Core Location technology will be maximised to determine your device’s position, altitude and orientation
- Key Log – Collect information about the keys used whilst your Mac was away
- Secret Screenshots & iSight Photos – Build a convincing criminal case using Secret Screenshots and iSight to capture the culprit on camera
- Remote Lock – Lock your Mac and activate a warning message to thieves
- Remote Wipe – Erase personal and private information from your Mac, no matter how far away it is
- Spoken Message – Type a message, and let your Mac read it aloud to the user
- SSH Tunneling – Hidden cleverly reverses the SSH Tunnel, letting you bypass firewalls and remotely access your Mac no matter what
3. Pombo
Free, comes with GPS Tracking
![]()
Pombo can help you recover your computer in the event it’s stolen. It works on Windows, GNU/Linux and macOS. How does it work? Pombo works silently in the background, hidden, and sends tracking information to a web server of your choice. If your computer is stolen, just log into your web server to get the latest file uploaded by Pombo, decrypt and hand it to the police. They will have all they need to catch the thief: IP address, date/time, nearby routers, screenshot, and even a photo of his/her face if you have a webcam !
4. Norton Mobile Security
Comes with GPS and SpyCam Features
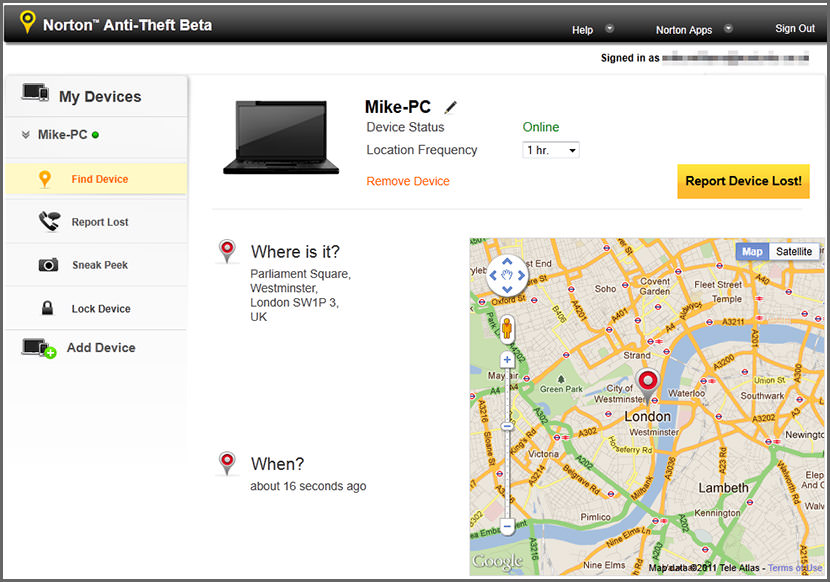
Norton Mobile Security helps you quickly lock and find your PC laptop, MacBook, tablet or smartphone – and protect the invaluable information contained on it – if it’s ever lost or stolen. And you can use any browser, anywhere, anytime to find out where it is and who has it and to remotely lock it. Features:
- Locate: Tracks and maps the location of your device when anyone uses it to go online so you will know if it is lost or stolen.
- Remote Lock: Securely locks your device to prevent strangers from using it or seeing your information.
- Lost Notification: Displays a customizable message to anyone who finds your missing device so you can make arrangements to get it back.
- Web Control: Works securely over the Internet, so you can easily track, locate, and lock your devices anytime, anywhere.
- Sneak Peek: Snaps photos of anyone or anything in front of your device then saves the images to the Norton Anti-Theft Web site to help you get back your device. (Webcam devices only)
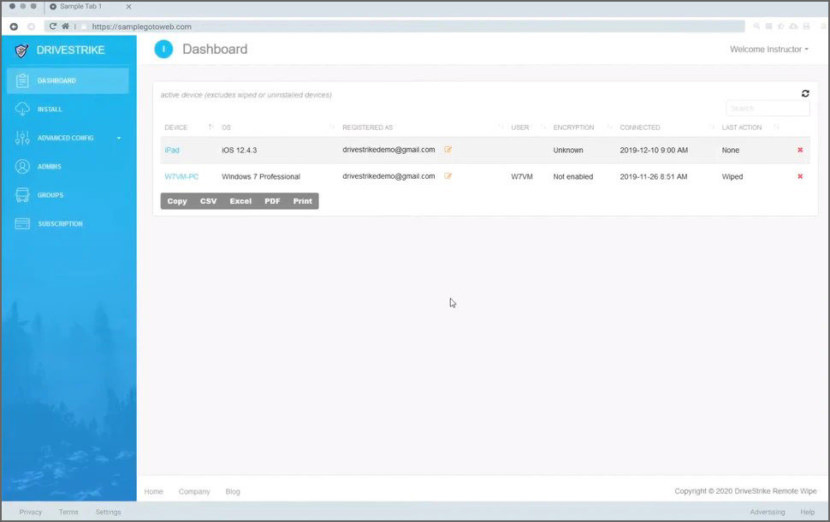
5. DriveStrike
Locate and Encrypt Features
DriveStrike is easy to use and straightforward to implement and manage. Their expert data protection support team is always available to answer your questions and help you install their services or manage your account and devices.
DriveStrike is HIPAA, GDPR, SOX, and DoD compliant. Protecting your data and devices has never been easier or more cost effective. If you have questions or need help understanding how best to protect your data please contact us.
- Locate – Find your lost or stolen device quickly and easily.
- Lock – Keep unauthorized users away from sensitive data – even if the device is lost.
- Wipe – Remotely delete personal or client data from any DriveStrike enabled device.
- Encrypt – Integrated BitLocker support or assistance with VeraCrypt.
6. Laptop Alarm
Alarm only
Yes, Laptop Alarm is a freeware, it doesn’t monitor or track your stolen laptop, it prevents. Once installed, Laptop Alarm will emit a LOUD ALARM on
- A/C Power Removal provided the battery is attached
- Mouse Removal
- Mouse Movement
- Attempt to Shutdown / Suspend
7. Absolute DDS [ Enterprise ]
Comes with GPS tracking
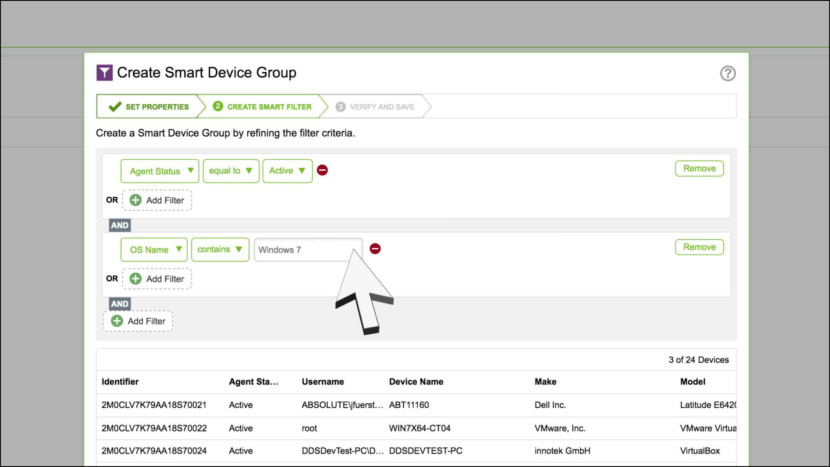
Absolute Data & Device Security (DDS), formerly Absolute Computrace, provides you with a persistent connection to all of your endpoints and the data they contain so you can deliver a digital learning experience while promoting a safer school environment and securing your IT assets. With Absolute DDS, it’s all about the connection. By maintaining a two-way connection with each device, you have the insight you need to assess risk and apply remote security measures so you can protect each endpoint, ensure a safer school environment, and recover stolen devices. This valuable insight is delivered through a cloud-based console that requires no additional IT infrastructure.
- Connect to absolute-protect.com, which establishes location of the computer.
- Calls phone number(s) you specify.
- No monitoring fee required.
- Saves owner info on hard disk that can prove ownership of the computer
- Survive hard disk formatting.
8. Inspire Trace
Comes with GPS tracking
[ Discontinued ] Inspice Trace is a laptop tracking and remote data destruction software. The security software emails you the precise location of your laptop. In addition, it lets you unrecoverably destroy your sensitive data in the laptop to protect the data from any unauthorized access. The highlights:
- Destroy data in stolen computer.
- Tamper-proof.
- Accurate and worldwide tracking.
9. PC PhoneHome
Comes with GPS tracking
[ Discontinued ] Once installed, PC PhoneHome will secretly send an invisible email message to an email address of your choice containing the physical location of your computer every time you get an Internet connection.
- Locates lost/stolen computer in virtually any country of the world.
- PC PhoneHome sends a stealth e-mail message containing its exact location
10. XTool Laptop Tracker
Comes with GPS and SpyCam Features
[ Discontinued ] What makes XTool Laptop Tracker unique is the camera function; more and more laptops are now made with built-in cameras due to the higher availability of bandwidth and the increasing demand for more personalized contacts. XTool Laptop Tracker has the ability to detect a camera connected to a laptop and can take a snapshot of the unauthorized user that is then relayed to the XTool Monitoring Center! Since statistics show that approximately 90% of laptop theft is committed by insiders (friends, employees, colleagues, etc), a picture of the unauthorized user not only quickly leads to the location of the thief but can be used as evidence in case the laptop is sold to a 3rd party!
XTool Laptop Tracker is a service designed to locate and recover lost or stolen laptops. The XTool Laptop Tracker service uses a smart agent designed to collect and transmit critical information needed to pinpoint its location when lost or stolen and/or to identify the unauthorized user in case of a theft.
- Laptop Camera Information, snap a pic of the theft
- GPS location detection
- Wifi Connection Information
- Guarantee Recovery or else Xtool will compensate your lost





I have my laptop, and all of my other mobile devises protected with Trackitback. This service has saved me tons of money by paying all the fees to get the item returned back to me.
My laptop was stolen on the weekend 3/6/2009 trying to see if HP has it’s own tracking divices it’s own computer. Touch Screen Pavilion never install a tracking decives never thought I will loss my Laptop.. Never the less HP Global Security Ivestigation team is Inform of my Notebook Stolen. The Police is slow but hope the investigation gos well… and they can track it. Any Information that will help just write it… Sad James :(
Hi James, did you say that HP does have its own tracking device for their computers or not?
Best Tool Or Software To Track And Recover Stolen Lapto?
I lost my lenovo laptop to thieves.The laptop seems to have been switched off. I didnt install any tracking software.Is it possible to recover or get it back?
“better safe than sorry”…
In case your laptop is stolen, having previously installed a backup software is really helpfull.
It enables you to revoer your data within a few clicks.
There are lots of products available (just type data backup in google), I’ve been using 77backup for a few years and I’m quite happy with it.
Tom
I’ve found a cool software.
You can remotly recover your files and then deleve all of them in case your laptop is stolen.
But I’am using even in day to day life. I recover my files while I’m away from home and my PC is not with me. Try this.
You can even get a camera images from your PC while you’re away
Maya.
what’s the name of the software?
I think you missed Prey on the list (preyproject.com). Its free and can be managed via a control panel!
Great work u r doing. My Hp compaq pressario cq61 got stolen. I hadnt installed a tracking system, how can i recover it or is there a way out?
Hi if anyone can help me i need a small gps tag that i can install into all my computers and that i can track using google maps.
Should you know of a product please mail me.
Thanks
Anton vd merwe South Africa
Hi Anton. You should try to use a battery-powered GPS asset tracker
If someone broke into your home and stole the laptop. Then there are chances of it being sold in the black market.
Luckily, a genuinely versatile and powerful track-and-recover
If the thief who stole your laptop connects it to the Internet, then this software will grab its IP
how to using dyndns to recover stolen laptop ubuntu?
One can only hope that the data on these laptops was encrypted
How far can companies go to track down stolen laptops?
Our anti-theft laptop software is the fastest way to get your lost or stolen … lets you track down the exact location of your laptop in real time as well as retrieve your data
Hello Sir
my laptop is missing so please help me my laptop mac id and ip Delly reporting but not searching location so please help me….
If you had no tracking software installed prior to have it missing, nothing can be done. Sorry about it. The rule of thumb is to always install a tracing software.
Tracking software is useless in most cases, because the thieves know not to connect it to the internet before wiping everything.
yes, but it is better to have some hope than none, just like buying an insurance policy, you’re going to die anyway, why waste money?
PC/home phone has horrible support. I purchased this product and they nave never once returned a telephone call nor have they ever responded to any of my numerous emails asking for specific customer support.
Hi I had recently lost my Lenovo laptop and I lost all my confidential and hard work data.
Can any one suggest how to track this laptop as I did not installed any tracking software or device is there any chance to recover.
Thanks in advance.
Does it mean that the 5 Laptop Theft Recovering
Software with GPS Location
Tracking and SpyCam methods are useless whether or not one installed a tracking app or device into their own laptop before it got stolen cause I didn’t install one in my HP Compaq before it got lost cause I initially didn’t know about it please help me am going mad about it.
You cannot track your laptop if you did not install the app before it was stolen, just like how you cannot track your car if no GPS tracking device was installed… unless you are from the CIA or NSA – world’s best spying and tracking agent.
Are you retarded?
https://us.norton.com/anti-theft/ is DISCONTINUED
Provide me the details of Physical Laptop Tracking.
my laptop is lost how to tracking
Hi, 2 of my phones have been stolen in the past year and I was wondering if it would be possible to recover them with my outlook and google accounts or with my old phone numbers?Thank you for your time and patience. Freddie McClaskey..
not possible unless you already have the app installed prior being stolen.
I need help my laptop is stolen
sir my laptop of thief just back time any time searched but not find Hp company
I LOST MY LAPTOP IT WAS STOLEN FROM ME MODEL NUMBER 80T7
A Lenovo laptop of my friend was stolen today and it has no windows but I need to find it, is it possible to find it?
All of this is absolutely useless if the laptop has to be connected to the internet, in order for the tracking to happen. I had my laptop stolen, the “find my device” option on iCloud is useless, because the thieves know better than to connect it to internet.
Software tracking systems are quite useless. IP address only gives you about city wide geo-location. imagine looking for the laptop where it’s somewhere in the city! Talk of looking for a needle in a haystack! GPS alone also cannot help you. You need full CIA level surveillance kinda system to do it. I recently found a cool solution online called the matrix blackbox gps laptop tracker.
Yea I second the matrix blackbox. First matrix blackbox is a laptop tracking hardware wired into your laptop and that you control via commands and NOT software. So there are absolutely zero chances that the thief will format/wipe it out. Second it uses GPS to triangulate the exact coordinates of your laptop location with an error of 5 meters or less. After getting to the area where your stolen laptop is, you pinpoint its exact location using WiFi. You simply command the balckbox which was wired in your laptop to activate its WiFi hotspot which you then connect to on your phone (remember this is your matrixblackbox wifi and not the thief’s Wifi) and it does this even if the thief has turned off the laptop. You follow the Wifi signal using the Wifi strength bars. The closer you are to the thief the stronger the signal you see on your phone’s WiFi bars. So you are actually not looking for a needle in a haystack but rather from here you pinpoint the exact location of your laptop with 99% accuracy. The best part…it has a spy feature and you can listen to anything that is being said around your laptop. So if you recognize one of the voices around it belonging to your “friend” or neighbor then alternatively you know who to go after.
mera laptop theft ho gaya mai kaise prapta kar sakta hu
please help me
My laptop got nicked and it does have tracking on. What if the thief re installs Windows 10. Will I still be able to track?
FYI – ESET Internet Security has this feature too.
My laptop has been stolen but keeps sending me gps location. How do I retrieve information about the thief ( IP address and logs).please help
please my laptop was not stolen I only downloaded the prey project on my laptop and mistakenly lock it please how do I unlock it
I lost my MacBook two weeks ago. The police and community have not been able to get it back yet. I didn’t have tracking hardware on it, and Find My iPhone isn’t working.
Is there a way to locate the laptop based on Serial Number? Please, I have a lot of valuable work on there.
I’m offering a $2,000 USD reward, possibly more, for it’s safe return.
Let me know.
Thank You.
I can track your laptop anytime any day. contact me for more enquiries.
my laptop have stolen. can u help me in this matter
I lost my laptop how can I you assist me to get it
Anyone help me …if someone stolen my laptop..after that educated theft going to format all hard drives and reinstall new windows operating systems ..then i installed all tracking softwares going to hell then how can we find my laptop ?
Here is my take on this. Don’t lose your laptop or device in the first place! It’s a far simpler thing to do (not lose it) than deal with all the ‘retrieval’ tools.
No point in installing those kind of software. People who steal laptops or devices in general know really well how do to it. Who is gonna turn it on as use it as it is? Only a chicken thief…
This list is good for consumers, but if you’re a business or government you want to go with