Category: Computer and Internet Security » VPN & ZTN
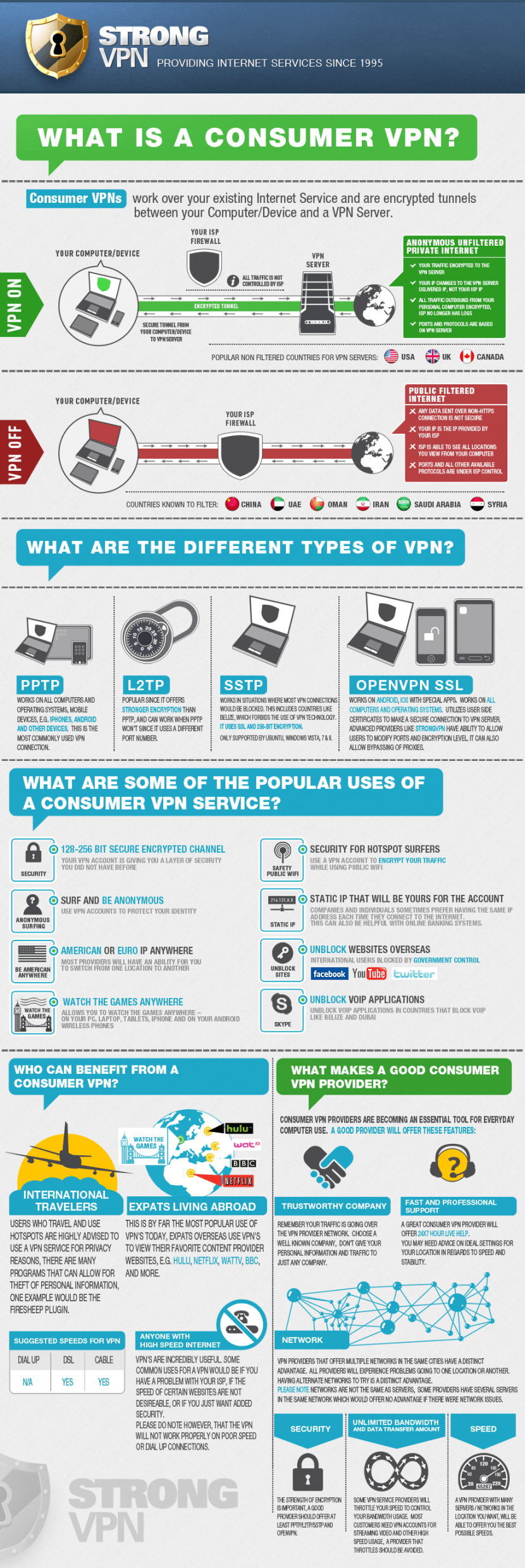
A virtual private network (VPN) is a private data network that makes use of the public telecommunication infrastructure(Internet), maintaining privacy through the use of a tunneling protocol and security procedures. The idea of the VPN is to give a company or a person the same capabilities at much lower cost by using the shared public infrastructure rather than a private one. In their case, they use a VPN to connect you to their servers in Europe and Asia.
Related Article 😍💰👉 Top 10 Free VPN Service With US UK Server [ Best Speed ]
- Protect your computer from internet attacks and intrusions.
- Prevents from unauthorized access your computers from internet.
- Filter network spam by their servers firewall system.
- Anonymize and secure all your Internet traffic and replace your ip address.
- Works with VOIP software, web browsing, e-mail, p2p, ftp, instant messaging, streaming, games etc.
If a free VPN is not your cup of tea or you find them unreliable, do give paid VPN a try. Remember this, free is not always free, if something is offered free, then you are the product.
- NordVPN [ The Best ] | Comes with P2P Servers, 100% no log.
Together with a VPN service, they create a connection called VPN. This is a secure connection that encrypts all your information and is not readable by anyone else so wherever you are your privacy is always maintained! The best part is, there is no software to install because most VPN works on all Platforms including Windows, Mac, Linux, IPhone etc using the built- in VPN software in your operating system. Without further ado, here are 9 Open Source VPN that can be used with VPN Gate.
1. Libreswan VPN
Libreswan is a free software implementation of the most widely supported and standardized VPN protocol based on (“IPsec”) and the Internet Key Exchange (“IKE”). These standards are produced and maintained by the Internet Engineering Task Force (“IETF”). Libreswan performs some additional hardening for the IKEv1 protocol that other implementations have not implemented. This is not a vulnerability and CVE-2016-5361 was issued erroneously.
2. OpenConnect
OpenConnect is an SSL VPN client initially created to support Cisco’s AnyConnect SSL VPN. It has since been ported to support the Juniper SSL VPN which is now known as Pulse Connect Secure. OpenConnect is released under the GNU Lesser Public License, version 2.1. Like vpnc, OpenConnect is not officially supported by, or associated in any way with, Cisco Systems, Juniper Networks or Pulse Secure. It just happens to interoperate with their equipment. Development of OpenConnect was started after a trial of the Cisco client under Linux found it to have many deficiencies:
- Inability to use SSL certificates from a TPM or PKCS#11 smartcard, or even use a passphrase.
- Lack of support for Linux platforms other than i386.
- Lack of integration with NetworkManager on the Linux desktop.
- Lack of proper (RPM/DEB) packaging for Linux distributions.
- “Stealth” use of libraries with dlopen(), even using the development-only symlinks such as libz.so — making it hard to properly discover the dependencies which proper packaging would have expressed
- Tempfile races allowing unprivileged users to trick it into overwriting arbitrary files, as root.
- Unable to run as an unprivileged user, which would have reduced the severity of the above bug.
- Inability to audit the source code for further such “Security 101” bugs.
Naturally, OpenConnect addresses all of the above issues, and more.
- Connection through HTTP proxy, including libproxy support for automatic proxy configuration.
- Connection through SOCKS5 proxy.
- Automatic detection of IPv4 and IPv6 address, routes.
- Authentication via HTTP forms.
- Authentication using SSL certificates — from local file, Trusted Platform Module and PKCS#11 smartcards.
- Authentication using SecurID software tokens (when built with libstoken)
- Authentication using OATH TOTP or HOTP software tokens.
- Authentication using Yubikey OATH tokens (when built with libpcsclite)
- UserGroup support for selecting between multiple configurations on a single VPN server.
- Data transport over TCP (HTTPS) or UDP (DTLS or ESP).
- Keepalive and Dead Peer Detection on both HTTPS and DTLS.
- Automatic update of VPN server list / configuration.
- Roaming support, allowing reconnection when the local IP address changes.
- Run without root privileges.
3. Openswan
Openswan is an IPsec implementation for Linux. It has support for most of the extensions (RFC + IETF drafts) related to IPsec, including IKEv2, X.509 Digital Certificates, NAT Traversal, and many others. Openswan has been the de-facto Virtual Private Network software for the Linux community since 2005. If you are running Fedora, Red Hat, Ubuntu, Debian (Wheezy), Gentoo, or many others, it is already included in your distribution! Just start using it right away. If you wish to download the source code directly, you can click the button below.
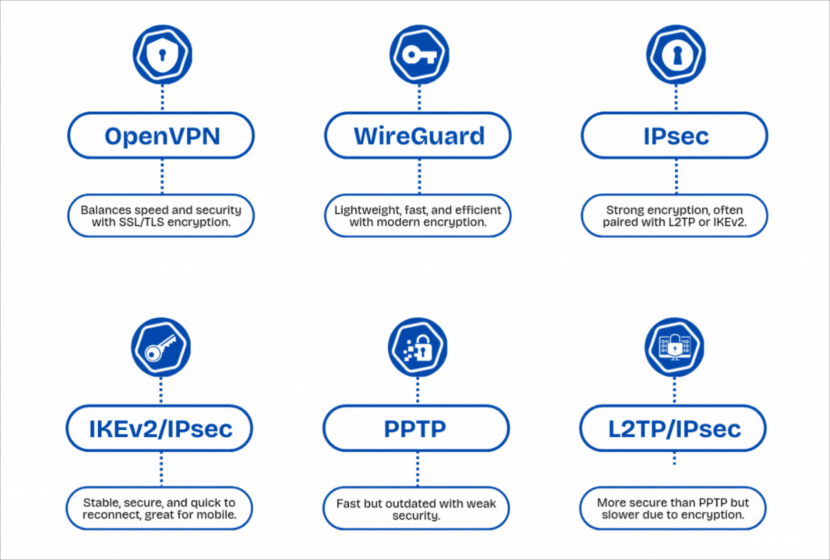
4. OpenVPN
OpenVPN is a full-featured open source SSL VPN solution that accommodates a wide range of configurations, including remote access, site-to-site VPNs, Wi-Fi security, and enterprise-scale remote access solutions with load balancing, failover, and fine-grained access-controls. Starting with the fundamental premise that complexity is the enemy of security, OpenVPN offers a cost-effective, lightweight alternative to other VPN technologies that is well-targeted for the SME and enterprise markets. With OpenVPN, you can:
- Tunnel any IP subnetwork or virtual ethernet adapter over a single UDP or TCP port,
- Configure a scalable, load-balanced VPN server farm using one or more machines which can handle thousands of dynamic connections from incoming VPN clients,
- Use all of the encryption, authentication, and certification features of the OpenSSL library to protect your private network traffic as it transits the internet,
- Use any cipher, key size, or HMAC digest (for datagram integrity checking) supported by the OpenSSL library,
- Choose between static-key based conventional encryption or certificate-based public key encryption,
- Use static, pre-shared keys or TLS-based dynamic key exchange,
- Use real-time adaptive link compression and traffic-shaping to manage link bandwidth utilization,
- Tunnel networks whose public endpoints are dynamic such as DHCP or dial-in clients,
- Tunnel networks through connection-oriented stateful firewalls without having to use explicit firewall rules,
- Tunnel networks over NAT.
- Create secure ethernet bridges using virtual tap devices, and
- Control OpenVPN using a GUI on Windows or macOS.
5. SocialVPN
SocialVPN is an open-source IPOP-based virtual network that connects your computers privately to your friends’ computers. It automatically maps online social network relationships using Jingle and XMPP to create your own user-defined peer-to-peer VPNs – with no hassle, and supporting unmodified TCP/IP applications.
In the SocialVPN, each user is in control of who their VPN connects to. To scale to large online social networks, SocialVPN employs a unique dynamic IPv4 address allocation/translation approach that avoids conflicts with local networks and devices outside a user’s social network. These are some of the ways you can use SocialVPN:
- Private data sharing – SocialVPN allows you to create private, end-to-end virtual IP networks connecting you to your friends. You can use these links to privately share data with your friends, using existing applications for file transfer and sharing.
- Mobile cloud computing – SocialVPN runs on Android devices and allows users to create VPNs connecting mobile devices as well as desktops, laptops and servers. It provides a basis for research and development on “social area networks” for data sharing and computational offloading.
- Decentralized OSNs – SocialVPN creates a communication overlay that can be used as a basis to design decentralized Online Social Networks (OSNs).
6. SoftEther VPN
SoftEther VPN (“SoftEther” means “Software Ethernet”) is one of the world’s most powerful and easy-to-use multi-protocol VPN software. It runs on Windows, Linux, Mac, FreeBSD and Solaris. SoftEther VPN is open source. You can use SoftEther for any personal or commercial use for free charge.
SoftEther VPN is an optimum alternative to OpenVPN and Microsoft’s VPN servers. SoftEther VPN has a clone-function of OpenVPN Server. You can integrate from OpenVPN to SoftEther VPN smoothly. SoftEther VPN is faster than OpenVPN. SoftEther VPN also supports Microsoft SSTP VPN for Windows Vista / 7 / 8. No more need to pay expensive charges for Windows Server license for Remote-Access VPN function. Features of SoftEther VPN
- Easy to establish both remote-access and site-to-site VPN.
- SSL-VPN Tunneling on HTTPS to pass through NATs and firewalls.
- Revolutionary VPN over ICMP and VPN over DNS features.
- Resistance to highly-restricted firewall.
- Ethernet-bridging (L2) and IP-routing (L3) over VPN.
- Embedded dynamic-DNS and NAT-traversal so that no static nor fixed IP address is required.
- AES 256-bit and RSA 4096-bit encryptions.
- Sufficient security features such as logging and firewall inner VPN tunnel.
- 1Gbps-class high-speed throughput performance with low memory and CPU usage.
- Windows, Linux, Mac, Android, iPhone, iPad and Windows Mobile are supported.
- SSL-VPN (HTTPS) and 6 major VPN protocols (OpenVPN, IPsec, L2TP, MS-SSTP, L2TPv3 and EtherIP) are all supported as VPN tunneling underlay protocols.
- The OpenVPN clone function supports legacy OpenVPN clients.
- IPv4 / IPv6 dual-stack.
- The VPN server runs on Windows, Linux, FreeBSD, Solaris and macOS.
- Configure All settings on GUI.
- Multi-languages (English, Japanese and Simplified-Chinese).
- No memory leaks. High quality stable codes, intended for long-term runs. They always verify that there are no memory or resource leaks before releasing the build.
- RADIUS / NT Domain user authentication function
- RSA certificate authentication function
- Deep-inspect packet logging function
- Source IP address control list function
- Syslog transfer function
7. strongSwan
strongSwan is a complete IPsec implementation for Linux 2.6, 3.x, and 4.x kernels. The focus of the project is on strong authentication mechanisms using X.509 public key certificates and optional secure storage of private keys on smartcards through a standardized PKCS#11 interface.
- Runs on Linux 2.6, 3.x and 4.x kernels, Android, FreeBSD, OS X and Windows
- Implements both the IKEv1 and IKEv2 (RFC 7296) key exchange protocols
- Fully tested support of IPv6 IPsec tunnel and transport connections
- Dynamical IP address and interface update with IKEv2 MOBIKE (RFC 4555)
- Automatic insertion and deletion of IPsec-policy-based firewall rules
- NAT-Traversal via UDP encapsulation and port floating (RFC 3947)
- Support of IKEv2 message fragmentation (RFC 7383) to avoid issues with IP fragmentation
- Dead Peer Detection (DPD, RFC 3706) takes care of dangling tunnels
- Static virtual IPs and IKEv1 ModeConfig pull and push modes
- XAUTH server and client functionality on top of IKEv1 Main Mode authentication
- Virtual IP address pool managed by IKE daemon or SQL database
- Secure IKEv2 EAP user authentication (EAP-SIM, EAP-AKA, EAP-TLS, EAP-MSCHAPv2, etc.)
- Optional relaying of EAP messages to AAA server via EAP-RADIUS plugin
- Support of IKEv2 Multiple Authentication Exchanges (RFC 4739)
- Authentication based on X.509 certificates or preshared keys
- Use of strong signature algorithms with Signature Authentication in IKEv2 (RFC 7427)
- Retrieval and local caching of Certificate Revocation Lists via HTTP or LDAP
- Full support of the Online Certificate Status Protocol (OCSP, RFC 2560).
- CA management (OCSP and CRL URIs, default LDAP server)
- Powerful IPsec policies based on wildcards or intermediate CAs
- Storage of RSA private keys and certificates on a smartcard (PKCS #11 interface)
8. Tinc VPN
tinc is a Virtual Private Network (VPN) daemon that uses tunnelling and encryption to create a secure private network between hosts on the Internet. tinc is Free Software and licensed under the GNU General Public License version 2 or later. Because the VPN appears to the IP level network code as a normal network device, there is no need to adapt any existing software. This allows VPN sites to share information with each other over the Internet without exposing any information to others. In addition, tinc has the following features:
- Encryption, authentication and compression – All traffic is optionally compressed using zlib or LZO, and LibreSSL or OpenSSL is used to encrypt the traffic and protect it from alteration with message authentication codes and sequence numbers.
- Automatic full mesh routing – Regardless of how you set up the tinc daemons to connect to each other, VPN traffic is always (if possible) sent directly to the destination, without going through intermediate hops.
- Easily expand your VPN – When you want to add nodes to your VPN, all you have to do is add an extra configuration file, there is no need to start new daemons or create and configure new devices or network interfaces.
- Ability to bridge ethernet segments – You can link multiple ethernet segments together to work like a single segment, allowing you to run applications and games that normally only work on a LAN over the Internet.
- Runs on many operating systems and supports IPv6 – Currently Linux, FreeBSD, OpenBSD, NetBSD, OS X, Solaris, Windows 2000, XP, Vista and Windows 7 and 8 platforms are supported. See their section about supported platforms for more information about the state of the ports. tinc has also full support for IPv6, providing both the possibility of tunneling IPv6 traffic over its tunnels and of creating tunnels over existing IPv6 networks.
9. Tcpcrypt
[ Discontinued ] Tcpcrypt is a protocol that attempts to encrypt (almost) all of your network traffic. Unlike other security mechanisms, Tcpcrypt works out of the box: it requires no configuration, no changes to applications, and your network connections will continue to work even if the remote end does not support Tcpcrypt, in which case connections will gracefully fall back to standard clear-text TCP.
Install Tcpcrypt and you’ll feel no difference in your everyday user experience, but yet your traffic will be more secure and you’ll have made life much harder for hackers.
So why is now the right time to turn on encryption? Here are some reasons:
- Intercepting communications today is simpler than ever because of wireless networks. Ask a hacker how many email passwords can be intercepted at an airport by just using a wifi-enabled laptop. This unsophisticated attack is in reach of many. The times when only a few elite had the necessary skill to eavesdrop are gone.
- Computers have now become fast enough to encrypt all Internet traffic. New computers come with special hardware crypto instructions that allow encrypted networking speeds of 10Gbit/s. How many of us even achieve those speeds on the Internet or would want to download (and watch) one movie per second? Clearly, they can encrypt fast enough.
- Research advances and the lessons learnt from over 10 years of experience with the web finally enabled us to design a protocol that can be used in today’s Internet, by today’s users. Their protocol is pragmatic: it requires no changes to applications, it works with NATs (i.e., compatible with your DSL router), and will work even if the other end has not yet upgraded to tcpcrypt—in which case it will gracefully fall back to using the old plain-text TCP. No user configuration is required, making it accessible to lay users—no more obscure requests like “Please generate a 2048-bit RSA-3 key and a certificate request for signing by a CA”. Tcpcrypt can be incrementally deployed today, and with time the whole Internet will become encrypted.






Free VPN proxy apple iPhone
salam,
man iPhon daram
shoma VPN peyda kardin ?
age darin adrssesho baram befrestin lotfan
Download Hotspot Shield Free VPN Software for Windows for secure and private browsing.
Hotspot Shield offers a free VPN solution with unlimited bandwidth for Windows and Mac.
Hotspot shield is the shittest VPN which is probably made by NSA.
Cyberghost and Nordvpn ;)
Every “free vpn” on app store or playstore are just changing ip, not more.
dns leak, everything… maybe secure to dont let your internet get ddosed, but you arent secure.
they all are saving logs, the “free vpns”.
Honestly, I never believe in this ‘no log’ thing. It is against the law not to do so, maybe what they will not provide the logs to authority if there are no crimes involved.
i miss you.my free vpn,where is she???
i need free vpn for iphone can u help me pls
Try betternet if you live in the us, if not you’ll have to pay
If you need a free vpn for iphone, try hotspot shield for iphone
dosnt work for me !?
how to get free VPN for macbook?
@changda
I think it is not free anymore. I do not encourage the usage of VPN unless you’re into hiding your traces.
GoTrusted Secure Tunnel Windows Version 2.3.4.5 is the best
hello
thankyou for this software
please send me a vpn username & password
I want a free vpn and easy connection for mac I can not connect BBC AND other sites
hi i can a free vpn for (mac osx) plase sending to email me. thanks.
i not can open eny site in iran
@darya – you need to enable VPN outside of Iran
i need vpn for mac
A free VPN service designed for use with Windows and Mac computers
I’m using Vpn one Click, it’s free for LInux, Windows and Android.
free your x, don’t give wrong info ! scammer
who can tell me how to use??
谢谢
thanks
I use to unblock bbc iplayer sometimes so many providers but this one seems to be fast and does the job for me here in spain.
There are a lot free VPN service online, just search Free VPN in Google, then you will see the lists. But there will be some limits with Free VPN, Maybe you can try some paid ones.
@andy: I use ivacy to unblock BBC iPlayer. but it has to be a UK server because iPlayer or BBC one isn’t available outside UK.
Great Article.
I was searching for a more secure VPN solution like OpenVPN for my VPS server but with free licence. I think SoftEther VPN is what I was looking for. I’m going to try it.
Thanks for the guide.
Well, All free VPNs are good because they provide free services :) I was wondering on google its show result about ReviewsDir, and there are many VPNs almost same from the list. I am using Spotflux which is best free VPN for iPhone.
Ivacy has the feature of OPEN vpn in their app as a feature.
Private Internet Access (PIA) VPN just went Open Source too!
This tutorial demystifies VPN deployment whether you’re setting up secure access for personal use or managing multiple endpoints, it delivers clarity.