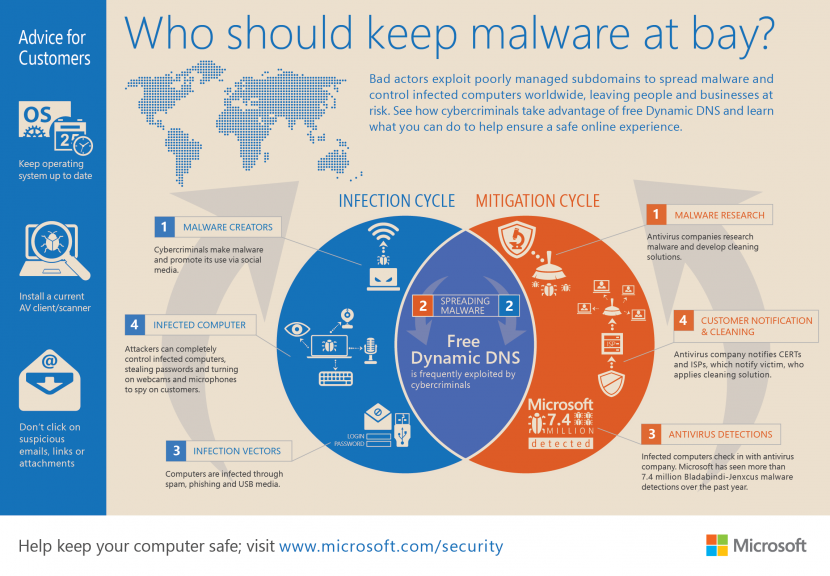
Is something not quite right with your Windows computer even when you have an antivirus installed? Are you being plagued by pop-up windows trying to get you to download security software or alerts claiming your PC isn’t secure? It appears like your antivirus could have been compromised, therefore a portable antivirus that works alongside your existing antivirus can provide a crucial second opinion on the health of your PC.
Related Article 😍💰👉 Top 10 Lightest Antivirus On Memory Usage, CPU, Low RAM – Norton vs Kasperky vs AVG etc
If your Microsoft Windows is infected by malware, chances are, your antivirus has been disabled by the virus or trojan. Uninstalling and reinstalling any antivirus is useless because the malware is programmed to disable it. This is where portable USB antivirus comes to the rescue. Two heads is better than one, having a second opinion from a different security software is better than none. Without further ado, here are the complete list of the best portable antivirus scanner that can be used without installation to scan and clean infected computers.
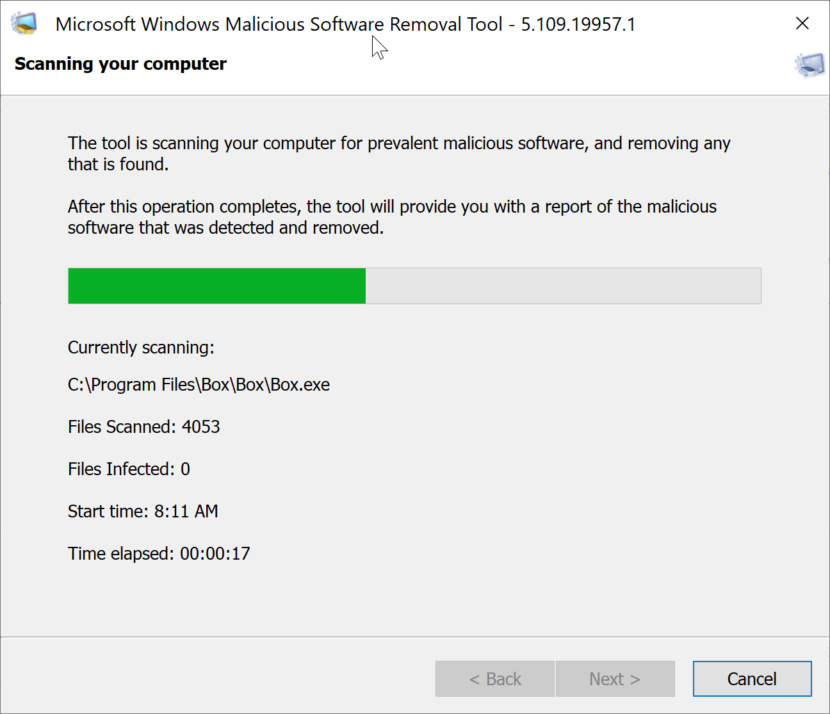
Windows Malicious Software Removal Tool (MSRT) helps keep Windows computers free from prevalent malware. MSRT finds and removes threats and reverses the changes made by these threats. MSRT is generally released monthly as part of Windows Update or as a standalone tool. MSRT targets prevalent malware families only. For comprehensive malware detection and removal, consider using Microsoft Safety Scanner or any other 3rd party tools listed below.
Pro & Con of Portable Antivirus
Portable standalone antivirus needs to be updated regularly; some antivirus allows you to download the database, while other requires you to download the entire software. Some standalone antivirus are not updated frequently, thus it might not be able to detect the latest malware. Here is the complete list of all portable antivirus, they are compatible with fully featured antivirus.
1. Microsoft Safety Scanner
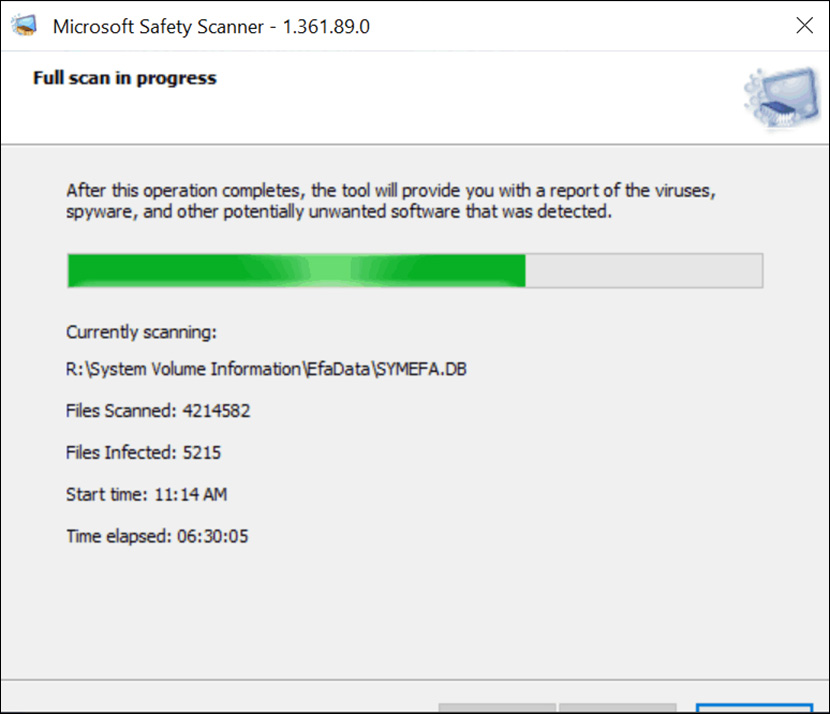
Do you think your PC has a virus? The Microsoft Safety Scanner is a free downloadable security tool that provides on-demand scanning and helps remove viruses, spyware, and other malicious software. It works with your existing antivirus software. Microsoft Safety Scanner expires 10 days after downloading. To re-run a scan with the latest anti-malware definitions, please download and run Microsoft Safety Scanner again.
This tool does not replace your anti-malware product. For real-time protection with automatic updates, use Windows Defender Antivirus on Windows or Microsoft Security Essentials on Windows 7. These anti-malware products also provide powerful malware removal capabilities.
2. Windows Malicious Software Removal Tool
Windows Malicious Software Removal Tool (MSRT) helps keep Windows computers free from prevalent malware. MSRT finds and removes threats and reverses the changes made by these threats. MSRT is generally released monthly as part of Windows Update or as a standalone tool available here for download.
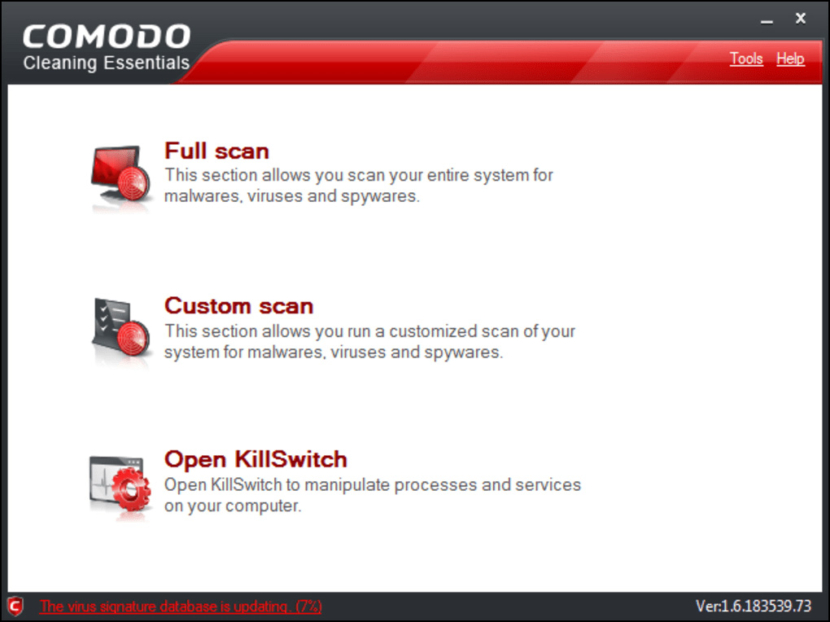
3. Comodo Cleaning Essentials
Comodo Cleaning Essentials (CCE) is a set of computer security tools designed to help users identify and remove malware and unsafe processes from infected computers. Designed as a portable application, the software requires no installation and can be run directly from removable media such as a USB key. CCE consists of two core technologies:
Fully featured malware scanner capable of unearthing and removing viruses, rootkits, hidden files and malicious registry keys hidden deep within a system. The scanner is highly configurable, uses the latest heuristic techniques to detect previously unknown viruses, features first-class malware removal capabilities and is capable of detecting hidden drivers and services loaded during system start-up.
- Instantly identify and stop every untrusted process running on an endpoint with a single click
- Powerful antivirus scanner capable of removing malware, rootkits, hidden files and malicious registry keys hidden deep within a system
- Forensic level stats and graphs allow internal processes and resource usage to be analyzed with unrivaled granularity
- Integration with Comodo cloud scanners provides real-time safety verdicts for unknown processes
- Perfect for ensuring network endpoints are totally clean of threats
- No installation required – can run direct from USB or user desktop via RDP
4. Kaspersky Virus Removal Tool
They’ve changed the way this software runs now, it is not portable anymore but still perform the scan as usual. Checks for known malware and software vulnerabilities on your PC – plus advises you on your PC’s security status with the free Kaspersky Virus Removal Tool. Kaspersky Virus Removal Tool uses Kaspersky Lab’s latest technologies – plus real-time access to cloud-based security information – to ensure it can scan your PC for the latest viruses and emerging threats.
A very simple quick scan for viruses and malware, during the download of Kaspersky Virus Removal Tool, there will be a download of Kaspersky Security Scan installation files, as well as Kaspersky Software Updater which is an integral part of Kaspersky Virus Removal Tool. Get FREE & quick help for your PC – download an efficient tool to clean up your computer from viruses, Trojans, malware, adware and more.
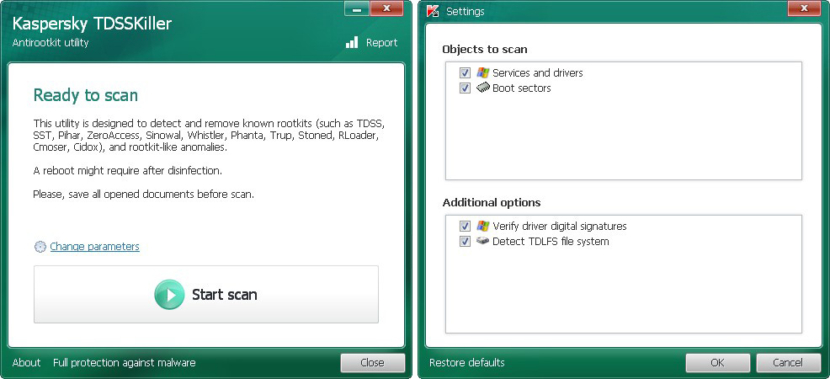
5. Kaspersky TDSSKiller
A rootkit for Windows systems is a program that penetrates into the system and intercepts the system functions ( Windows API ). It can effectively hide its presence by intercepting and modifying low-level API functions. Moreover it can hide the presence of particular processes, folders, files and registry keys.
Some rootkits install its own drivers and services in the system (they also remain “invisible”). Remember, TDSSKiller is not a substitute for anti-virus or Internet security software protection. To keep your computer and devices secure, you should install Internet security software.
List of malicious programs: Rootkit.Win32.TDSS, Rootkit.Win32.Stoned.d, Rootkit.Boot.Cidox.a, Rootkit.Boot.SST.a, Rootkit.Boot.Pihar.a,b,c, Rootkit.Boot.CPD.a, Rootkit.Boot.Bootkor.a, Rootkit.Boot.MyBios.b, Rootkit.Win32.TDSS.mbr, Rootkit.Boot.Wistler.a, Rootkit.Win32.ZAccess.aml,c,e,f,g,h,i,j,k, Rootkit.Boot.SST.b, Rootkit.Boot.Fisp.a, Rootkit.Boot.Nimnul.a, Rootkit.Boot.Batan.a, Rootkit.Boot.Lapka.a, Rootkit.Boot.Goodkit.a, Rootkit.Boot.Clones.a, Rootkit.Boot.Xpaj.a, Rootkit.Boot.Yurn.a, Rootkit.Boot.Prothean.a, Rootkit.Boot.Plite.a, Rootkit.Boot.Geth.a, Rootkit.Boot.CPD.b, Backdoor.Win32.Trup.a,b, Backdoor.Win32.Sinowal.knf,kmy, Backdoor.Win32.Phanta.a,b, Virus.Win32.TDSS.a,b,c,d,e, Virus.Win32.Rloader.a, Virus.Win32.Cmoser.a, Virus.Win32.Zhaba.a,b,c, Trojan-Clicker.Win32.Wistler.a,b,c, Trojan-Dropper.Boot.Niwa.a, Trojan-Ransom.Boot.Mbro.d, e, Trojan-Ransom.Boot.Siob.a, Trojan-Ransom.Boot.Mbro.f.
6. Symantec Norton Power Eraser
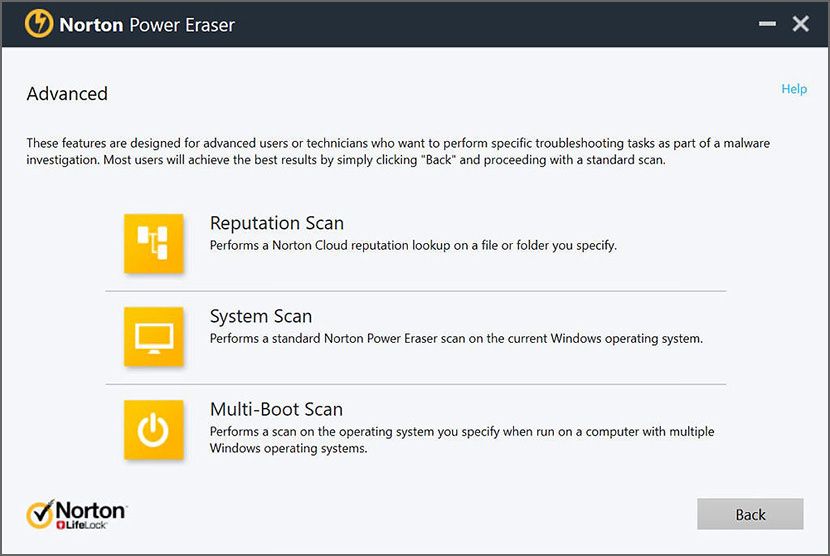
Eliminates deeply embedded and difficult to remove crimeware that traditional virus scanning doesn’t always detect. Norton Power Eraser is a free tool that can be downloaded and run to remove threats from your computer. You can run this tool to scan for threats even if you have a Symantec product, or any other security product. If you cannot start the computer in Normal mode, you can run this tool in Safe mode. Norton Power Eraser is easy to download, and scans your computer quickly to detect the most aggressive computer viruses. You don’t need to install this tool.
The Norton Power Eraser tool is compatible with computers running Microsoft Windows operating systems only. It does not work with computers running on macOS. Norton Power Eraser uses aggressive methods to detect threats, and there is a risk that it can select some legitimate programs for removal. You should carefully review the scan results page before removing files.
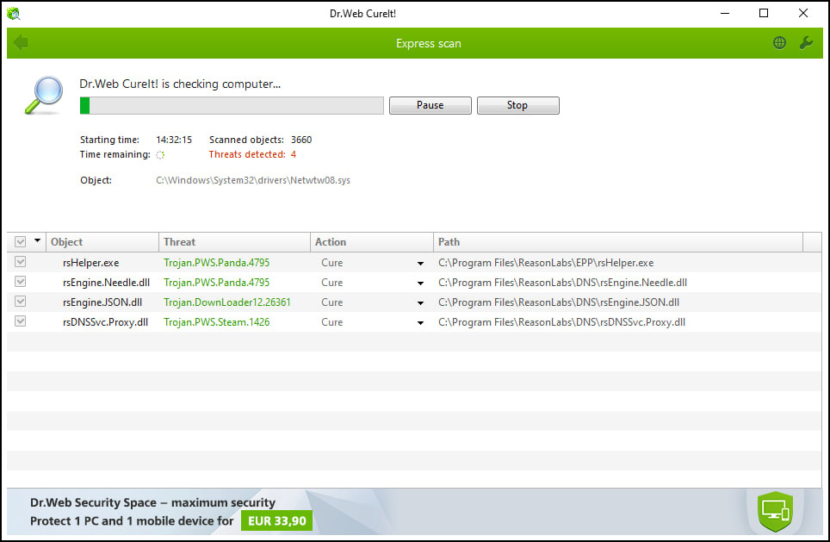
7. Dr.Web CureIt!
Run Dr.Web CureIt!® (no need to install it) is Russian antivirus that quickly scan your computer and cure it of any malicious objects. Dr.Web CureIt! is an indispensable tool for curing computers running Microsoft Windows. Dr.Web CureIt! detects and neutralizes viruses, rootkits, Trojan horses, spyware, and other malicious objects that have gone undetected by your anti-virus software.
The Dr.Web CureIt! utility will cure an infected system once, but it is not designed to provide your PC with real-time protection from viruses. The utility available on their website always features the latest virus definitions, but its virus databases aren’t updated automatically. Included in Dr.Web CureIt! is a set of virus databases that are only current until a new update is released (usually one or more times per hour).
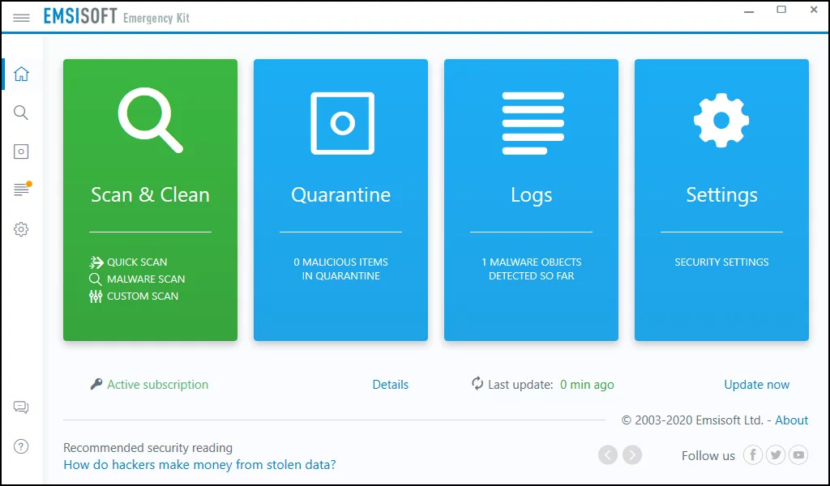
8. Emsisoft Emergency Kit
The Emsisoft Emergency Kit contains a collection of programs that can be used without software installation to scan for malware and clean infected computers: Emsisoft Emergency Kit Scanner and Emsisoft Commandline Scanner. The Emsisoft Emergency Kit Scanner includes the powerful Emsisoft Scanner complete with graphical user interface.
Scan the infected PC for Viruses, Trojans, Spyware, Adware, Worms, Dialers, Keyloggers and other malicious programs. Emsisoft Emergency Kit is free for private use. For commercial use, please have a look at their Emsisoft Emergency Kit Pro page.
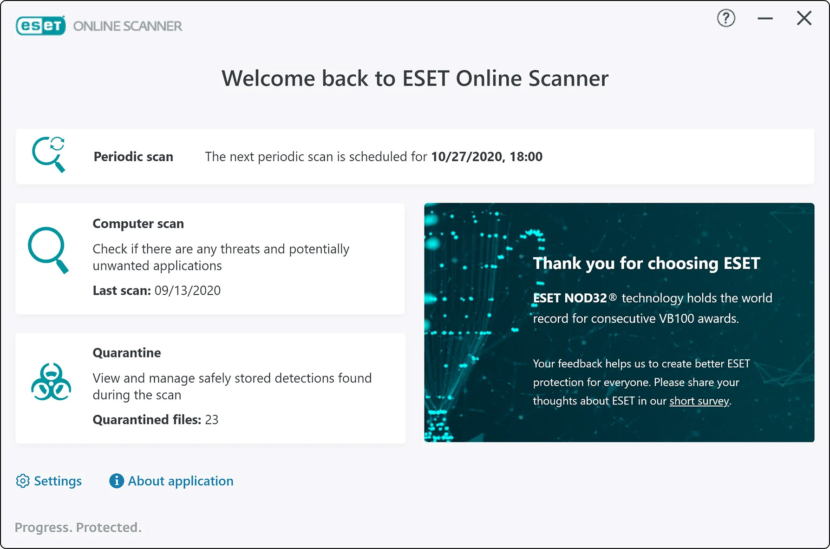
9. ESET Free Online Scanner
Detect and remove malware on your PC with a powerful and user-friendly tool that uses the same ThreatSense® scanning technology and signatures as ESET Smart Security and ESET NOD32 Antivirus — just by using your web browser. One-time scan to remove malware and threats from your computer for FREE.
- Smart way to test your antivirus – Easy-to-use tool that can run alongside any existing antivirus
- Comprehensive malware detection – Find and remove viruses, Trojans, spyware, phishing and other internet threats
- FREE and easy-to-use tool – No commitment, no registration and completely free one-time scan
- Periodic scanning of your device – Regular and automatic monthly check for infections and suspicious applications
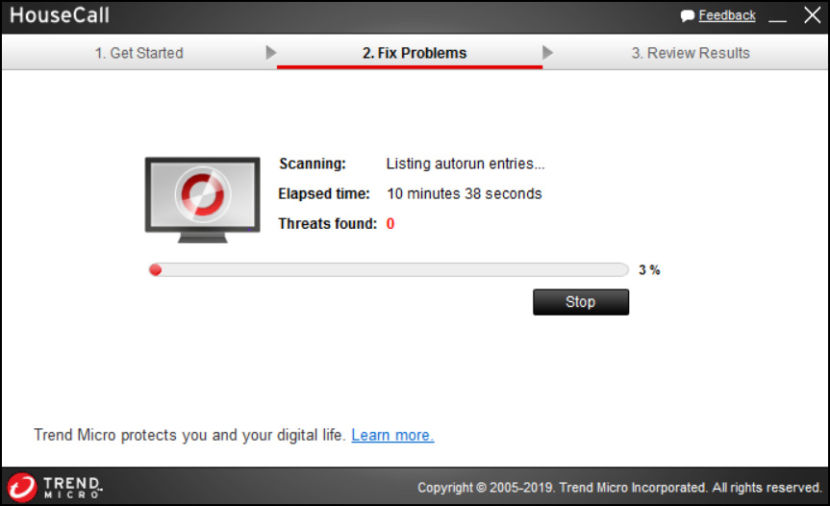
10. TrendMicro HouseCall
HouseCall is Trend Micro’s highly popular on-demand antivirus software scanner for identifying and removing viruses, trojans, worms, unwanted browser plugins, and other malicious software. Detect and fix viruses, worms, spyware, and other malicious threats for free. Start a free scan for your platformHouseCall Antivirus includes the following features:
- Stand-alone eliminates compatibility issues associated with browser-activated scanners
- Smart Scan delivers the latest antivirus protection while reducing download times
- Enhanced Detection and Cleanup addresses rootkits and other sophisticated threats
- Enhanced Scanning performance speeds threat detection
- Vulnerability scans find threats on other devices connected to your home network
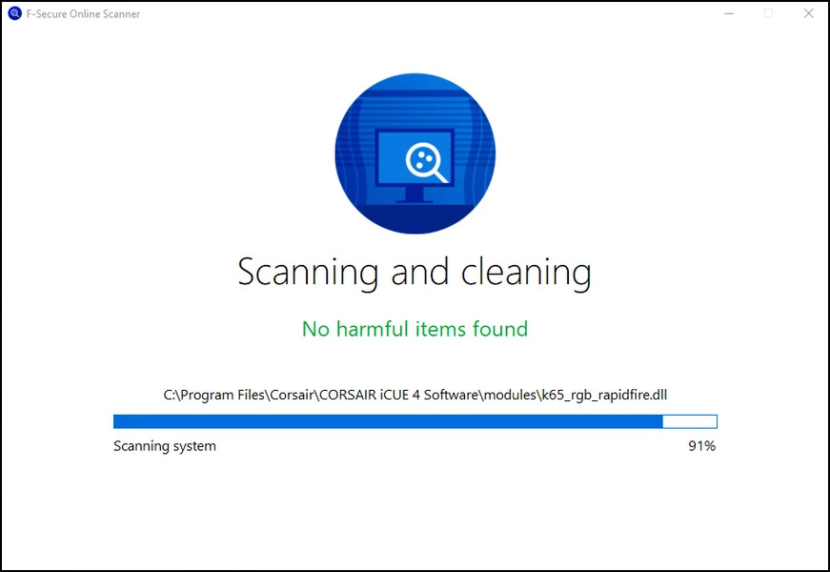
11. F-Secure Online Scanner
F‑Secure Online Scanner helps to get rid of viruses and spyware that may cause problems on your PC, and it works even if you have other security software installed on your computer. F‑Secure Online Scanner is easy to use with just a couple of clicks: just download it and run it. It does not leave anything on your PC. Virus worries? Run a scan for free and get rid of malware.
- Find and remove viruses, malware and spyware on your PC
- Easy to use, doesn’t leave anything on your computer
- Works with any other security software installed
- Completely free to run and use
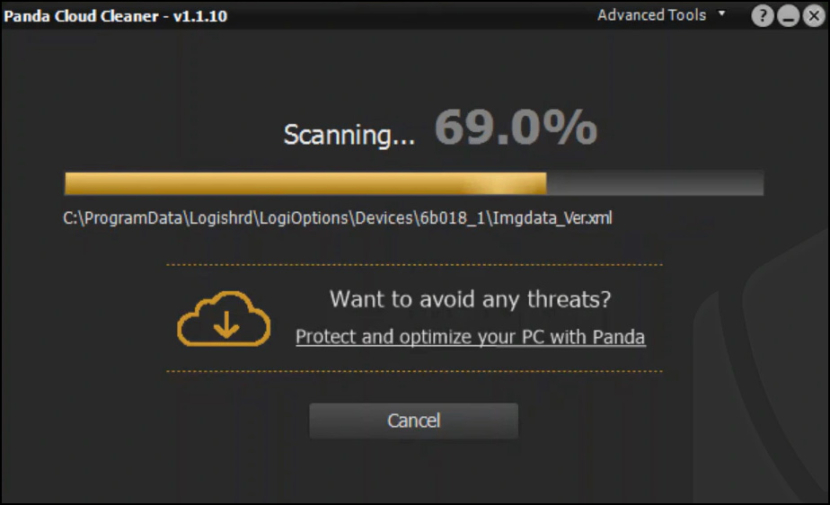
12. Panda Cloud Cleaner
Panda Cloud Cleaner is an advanced disinfector based on Collective Intelligence (scanning in-the-cloud) that detects malware that traditional security solutions cannot detect. Disinfect your computer with Panda Cloud Cleaner, they help you keep viruses at bay. Greater detection capacity than traditional antivirus solutions thanks to its latest generation technologies.
Online detection of all types of malware, vulnerabilities and unknown threats. It is easy to use from your browser and always up-to-date against the latest threats. A free report about threats detected and the status of the security protection installed on your computer.
13. ClamWin Portable
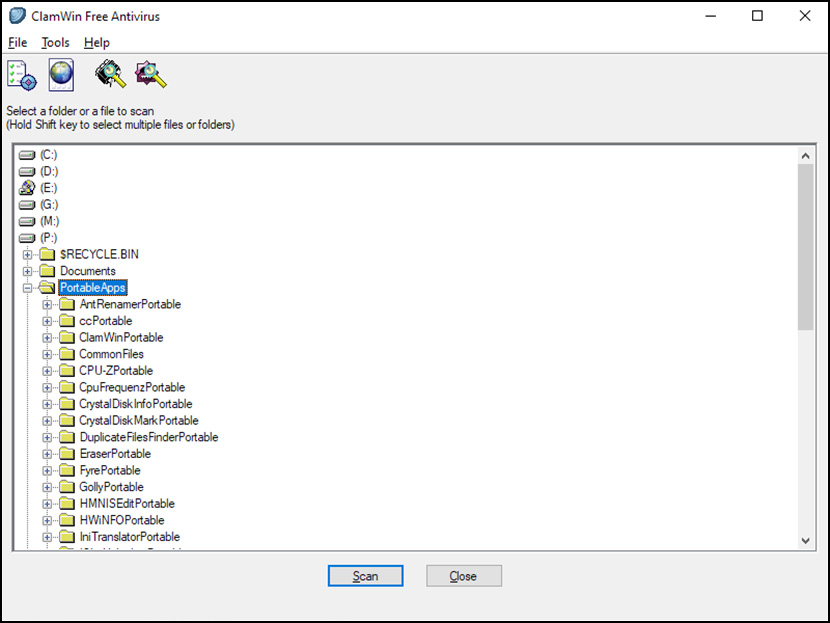
ClamWin is a Free Antivirus for Microsoft Windows. It provides a graphical user interface to the Clam AntiVirus engine. It features high detection rates for viruses and spyware, regular antivirus updates from the ClamAV team, and a standalone antivirus scanner. ClamWin allows for manually scanning individual files, folders, or drives but does not include an always-on background scanner.
14. Sophos Scan & Clean
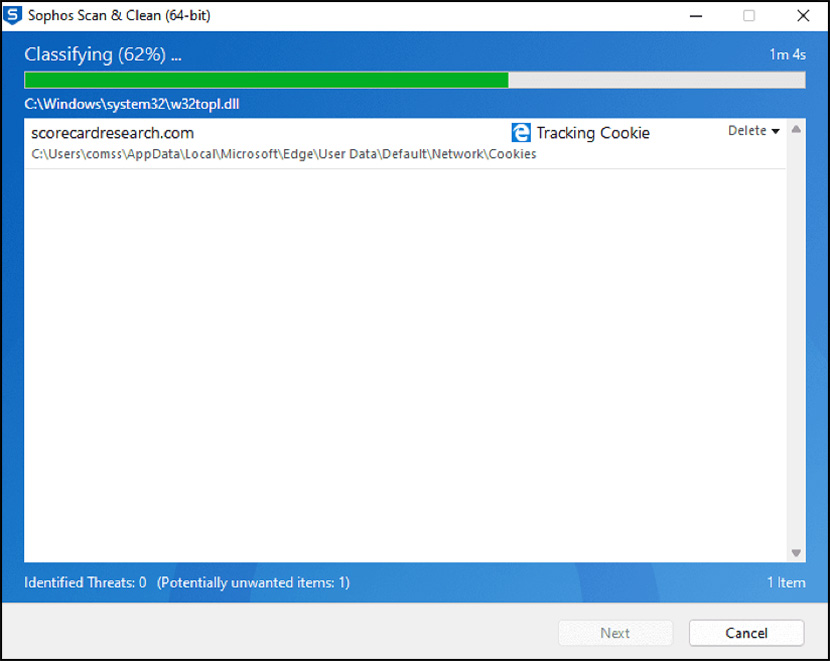
Using cutting edge technology found in their enterprise-grade software, this powerful tool detects all types of malicious software on your computer—including viruses, spyware, rootkits and Conficker—and returns it to a working state.
Sophos Scan & Clean is a free, no-install, second-opinion virus removal scanner designed to rescue computers that have become infected with advanced zero-day malware, spyware, Trojans, rootkits, and other threats capable of evading real-time protection from up-to-date antivirus software.
The tool has direct access to virus data from SophosLabs, their global network of threat researchers, ensuring that even the very latest viruses are detected and removed. And it works alongside your existing antivirus. Their free Virus Removal Tool is a quick and easy way to find and get rid of any threats lurking on your computer. Their tool identifies and cleans up infections your antivirus might have missed.
Sophos Scan & Clean removes viruses and threats while the OS is running and blocks re-infection by protecting registry keys and file locations. Plus, thanks to proprietary cloud technology, Sophos Scan & Clean is always up to date – no need to re-install to get updates each time the program is run.
Proprietary Cloud-Assisted Miniport Hook Bypass technology allows Scan & Clean to defeat rootkit and bootkit hooks for any hard disk driver. Behavioral Scans automatically find and remove programs and binaries that look and act like malware; probing the system for characteristic reputation anomalies, origin and relation to memory, file and registry objects, structure anomalies, impersonation, tampering, visibility, activity, boot survivability and uninstallation abilities.
- Removes viruses, Conficker, rootkits, and fake antivirus
- Supports Windows XP SP2 and up
- Works alongside your existing antivirus
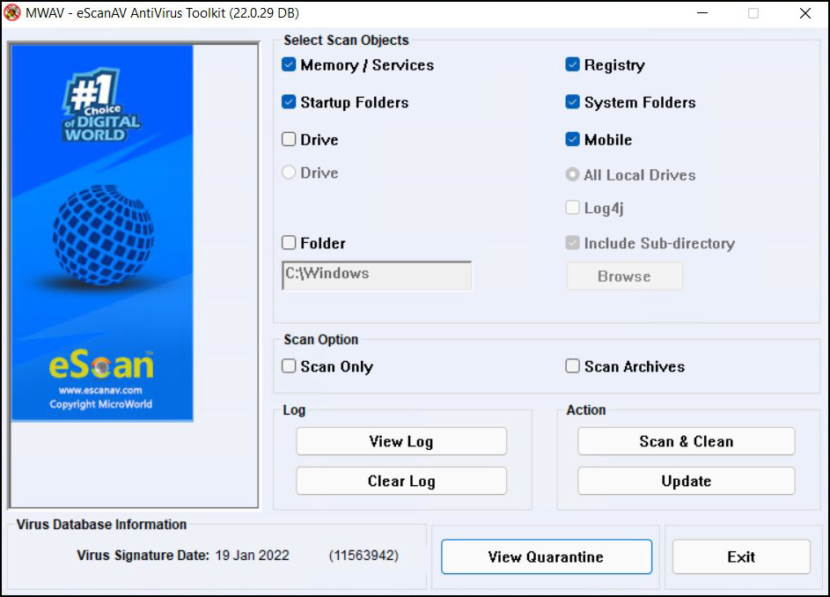
15. eScan Anti-Virus Toolkit
eScanAV Antivirus Toolkit (MWAV) is a FREE utility that enables you to scan and clean Viruses, Spyware, Adware and any other Malware that may have infected your computer. The eScanAV Antivirus Toolkit (MWAV) requires no installation and can be run directly from anywhere, on your computer, USB Drive or from a CD ROM. It can also run if you already have other Anti-Virus software installed on your computer.
The eScanAV Antivirus Toolkit (MWAV) also gets updated on a daily basis with the latest updates to detect spyware and adware released recently, plus the engine is constantly being improved for faster and intelligent detections. Free eScan Antivirus Toolkit Download for Windows. Scan for Viruses, Spyware and Adware in your computer. Just download and run. No installation of this software required.
16. GMER
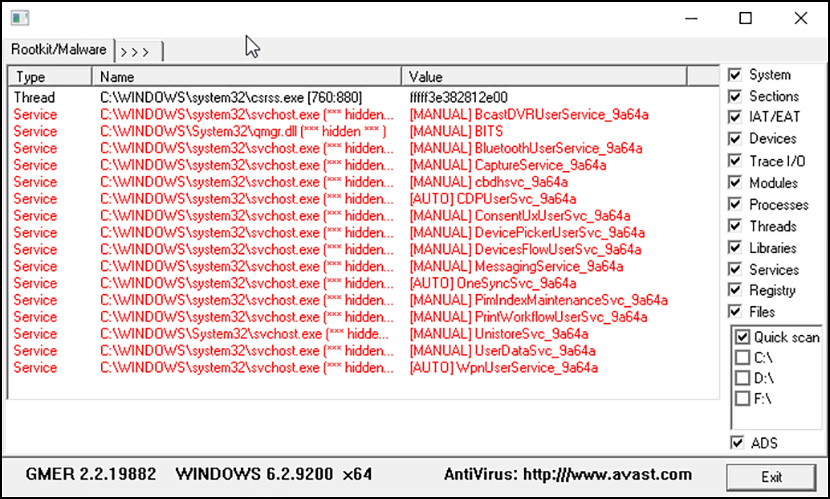
GMER is an application that detects and removes rootkits. It scans for hidden processes, hidden threads, hidden modules, hidden services, hidden files, hidden disk sectors (MBR), hidden Alternate Data Streams, hidden registry keys, drivers hooking SSDT, drivers hooking IDT, drivers hooking IRP calls and inline hooks.
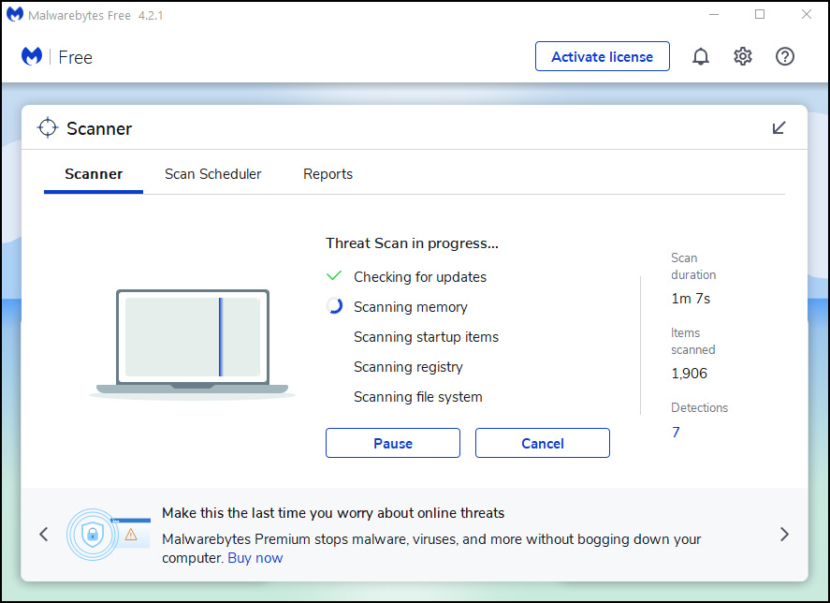
17. Malwarebytes Free Virus Scanner
Scan and remove viruses and malware from your device with our free virus scanner and AV scanner. Our virus scan supports all devices – Windows, macOS, Android and iOS. Malwarebytes Anti-Rootkit drills down and removes even deeply embedded rootkits. Malwarebytes Anti-Rootkit is cutting edge technology for detecting and removing the nastiest malicious rootkits. Removes and repairs the latest rootkits and the damage they cause.
A rootkit is hard to detect, because it hides deep in your device’s operating system. Many rootkits run on a higher level of privilege than most cybersecurity software which is one reason why they’re so difficult to detect. Rootkits can hijack or subvert less sophisticated security software like traditional antivirus solutions. Rootkit symptoms
- Slow computer performance – Rootkits drain memory which results in sluggish computer performance.
- Web browser redirects – You’re seeing weird web browser behavior like Google link redirects or unrecognized bookmarks.
- Windows error messages – You’re getting Windows error messages (“The Blue Screen of Death”) and are constantly rebooting.
- Personal information is stolen – Your credit card, social security number, and user passwords are stolen.
- Anti-virus isn’t working – Your antivirus software is suddenly deactivated.
18. AntiSpy
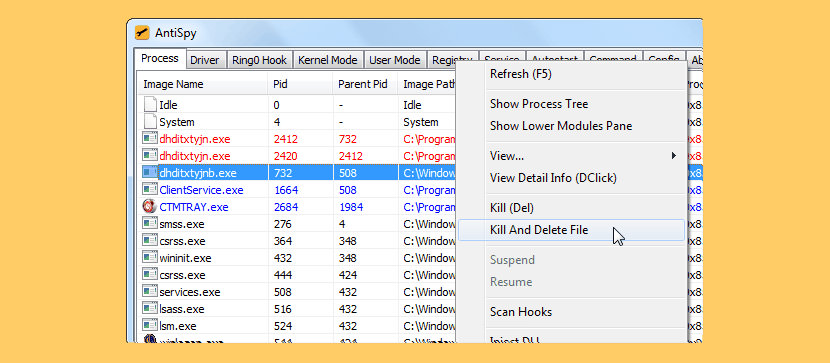
AntiSpy is a free but powerful anti virus and rootkits toolkit.It offers you the ability with the highest privileges that can detect,analyze and restore various kernel modifications and hooks.With its assistance,you can easily spot and neutralize malwares hidden from normal detectors.
19. NoVirusThanks Anti-Rootkit
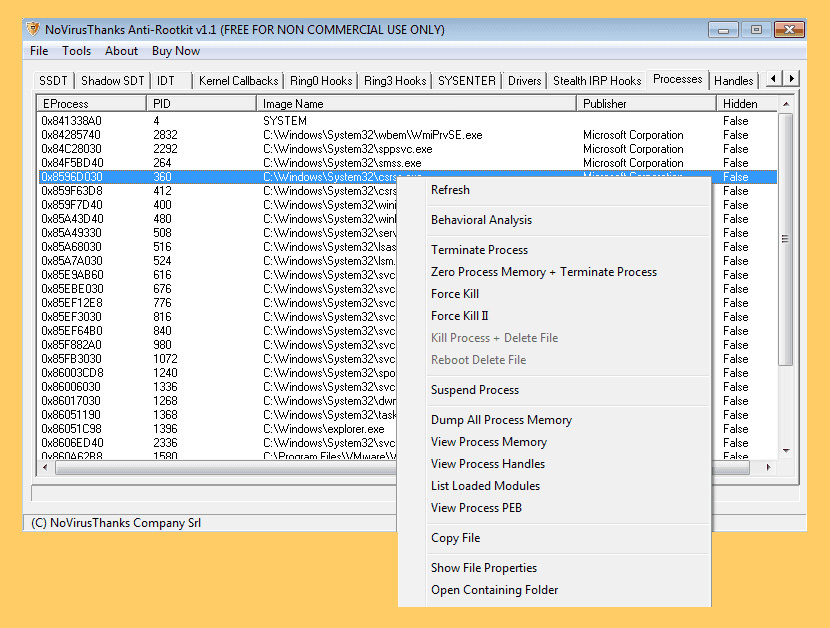
NoVirusThanks Anti-Rootkit is a sophisticated low-level system analysis tool whose main goal is to detect the presence of malware and rootkits. Hidden processes, hidden drivers, stealth DLL modules, code hooks etc. are just a few of the objects which can be detected in user space and system memory.
NoVirusThanks Anti-Rootkit detect undetectable stealth malware is a must-have for anyone seeking true 32-bit Windows NT kernel security and system threat analysis. The vast detection range of industry standard rootkits is truly amazing especially without compromising system stability even in the most hostile, malware-plagued environments.
20. Microsoft RootkitRevealer
RootkitRevealer is an advanced rootkit detection utility. It runs on Windows XP (32-bit) and Windows Server 2003 (32-bit), and its output lists Registry and file system API discrepancies that may indicate the presence of a user-mode or kernel-mode rootkit. RootkitRevealer successfully detects many persistent rootkits including AFX, Vanquish and HackerDefender (note: RootkitRevealer is not intended to detect rootkits like Fu that don’t attempt to hide their files or registry keys). If you use it to identify the presence of a rootkit please let us know!
The reason that there is no longer a command-line version is that malware authors have started targeting RootkitRevealer’s scan by using its executable name. We’ve therefore updated RootkitRevealer to execute its scan from a randomly named copy of itself that runs as a Windows service. This type of execution is not conducive to a command-line interface. Note that you can use command-line options to execute an automatic scan with results logged to a file, which is the equivalent of the command-line version’s behavior.
21. Spy DLL Remover
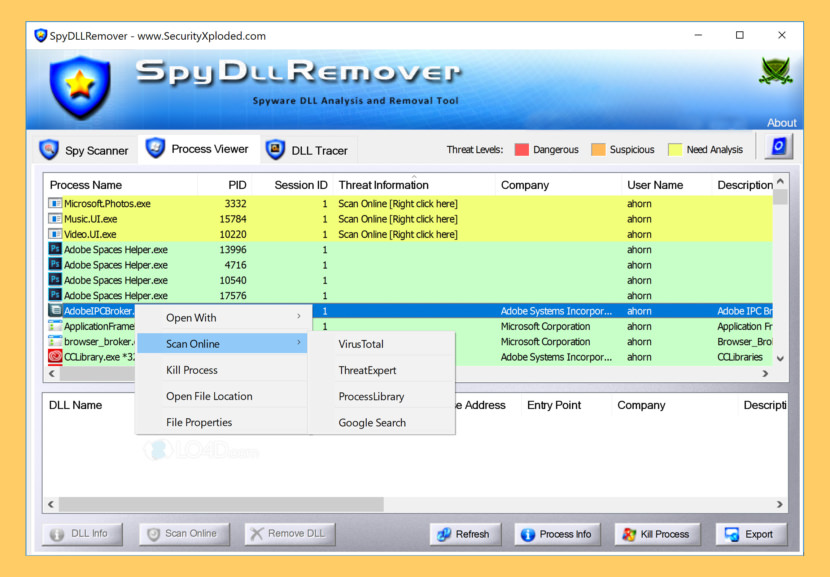
SpyDllRemover is the specialized tool for detecting Spyware & Hidden Rootkit Dlls in the System. In addition to Spyware Dlls, it can also detect user-land Rootkit processes using multiple Anti-Rootkit techniques. It uses Heuristic analysis and ‘Online Threat Verification’ for deeper analysis of unknown Malware Threats.
- Advanced Spyware Scanner: Detects Hidden User-land Rootkit processes as well as suspicious/injected Dlls within running Processes.
- Hidden Rootkit Detection & Removal: Uses multiple techniques to detect user-land Rootkits such as Direct NT System Call Implementation, Process ID Brute force Method (PIDB) as first used by BlackLight, and CSRSS Process Handle Enumeration Method.
- Unique ‘Advanced DLL Ejection’: This is one of the Advanced & Unique feature of SpyDLLRemover used to completely remove the injected DLL from Remote Process.
- Sophisticated Auto Analysis: Dll & Process Heuristics to help in Identification of known as well as Unknown Threats.
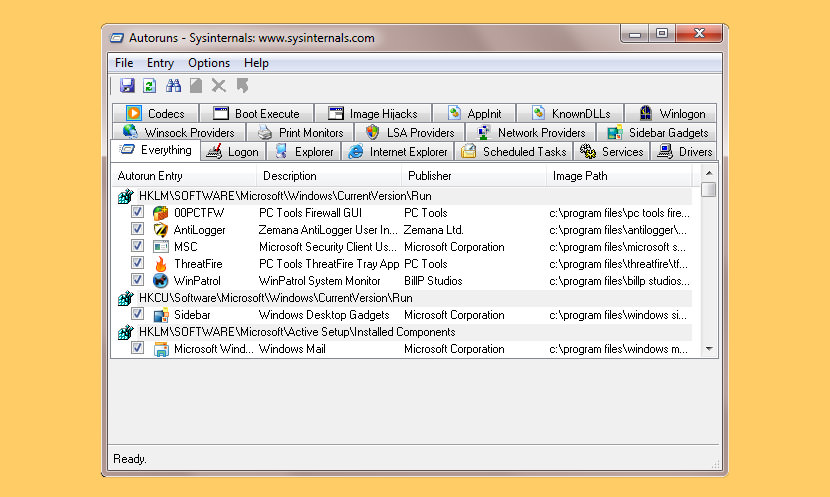
22. RKill
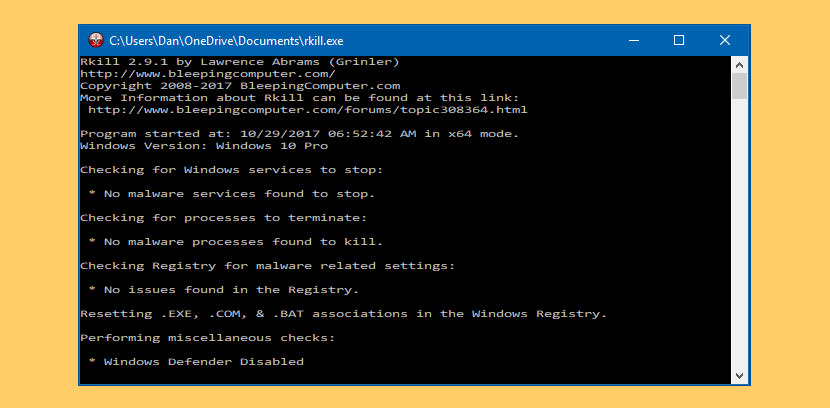
RKill is a program that was developed at BleepingComputer.com that attempts to terminate known malware processes so that your normal security software can then run and clean your computer of infections. When RKill runs it will kill malware processes and then remove incorrect executable associations and fix policies that stop us from using certain tools. When finished it will display a log file that shows the processes that were terminated while the program was running.
23. SuperAntiSpyware Free
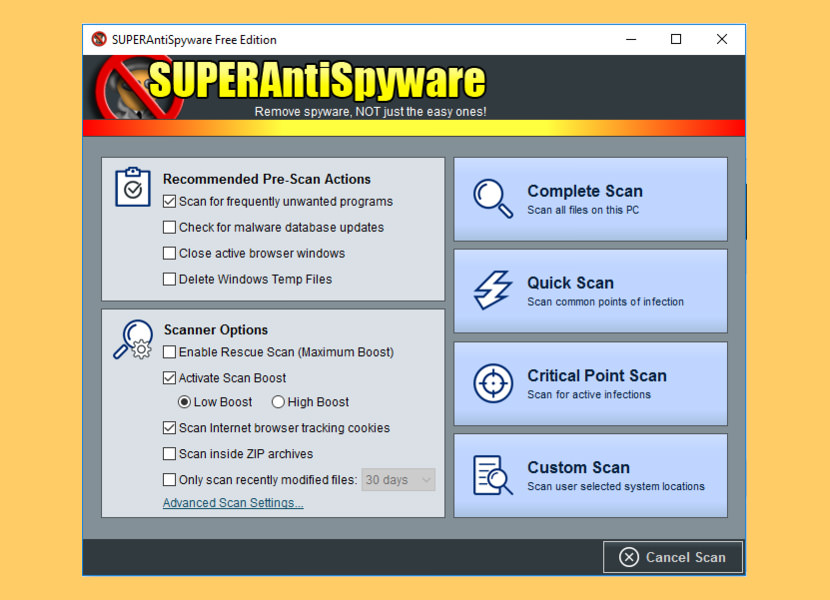
Protect your PC from malicious threats from malware, spyware, trojans, and more. SUPERAntiSpyware specializes in unique and hard-to-find malware, identifying and removing instances of malicious threats including Spyware, Adware, Trojans, Worms, Ransomware, Hijackers, Parasites, Rootkits, KeyLoggers, and more.
Protect your computer from threats: spyware, adware, trojans, ransomware, PUPs, hijackers, and more. Get the most up-to-date protection with database updates 2-4x a day and in-depth system scanning and removal tools. Install their lightweight program that won’t slow down your PC, and works with, not against, your antivirus.
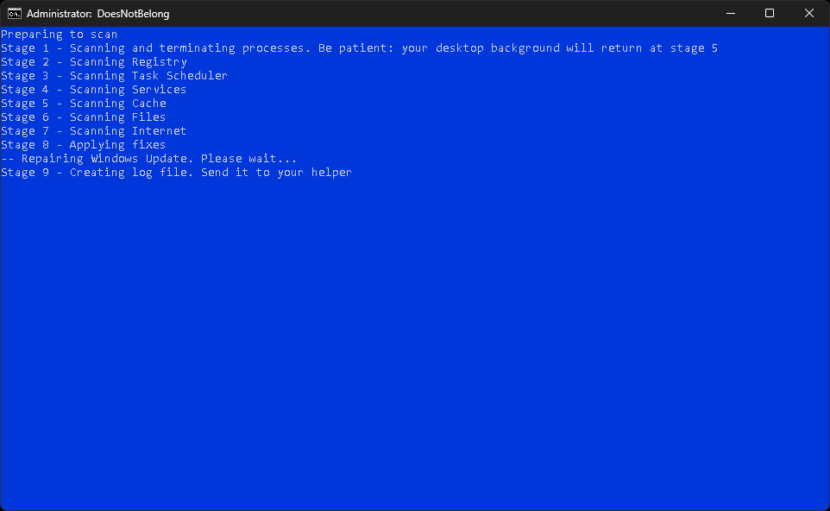
24. DoesNotBelong
DoesNotBelong is a lightweight and specialized program for additional system scanning that compliments the main antivirus. It helps to identify threats not detected by the main antivirus and may be useful if you suspect an infection despite a “clean” scan result from other scanners.
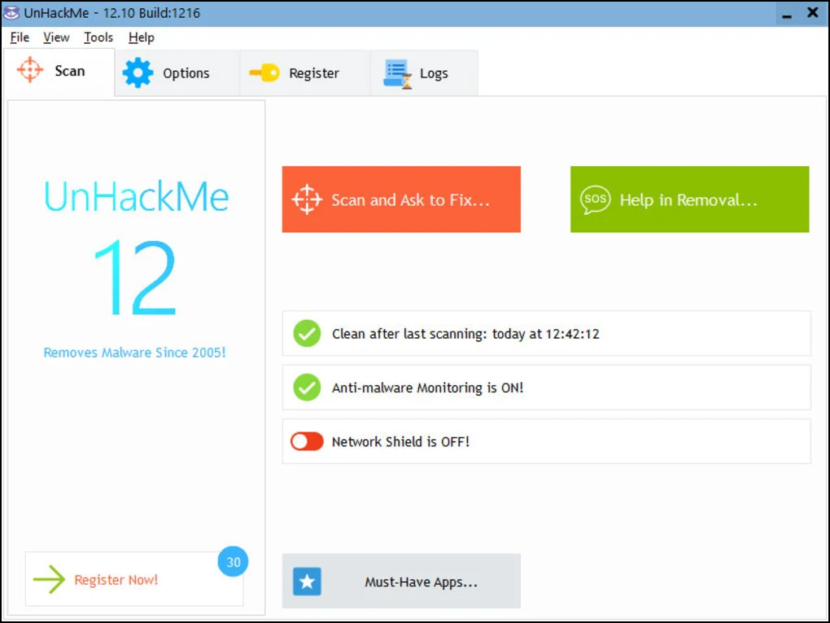
25. UnHackMe
[ Not Free Anymore ] UnHackMe was initially created as anti-rootkit software (2005), but currently eliminates the following types of malicious software – Search redirecting, Popup ads, Potentially unwanted programs (PUPs), Unwanted processes, Slow browsing, Rootkits, Trojans, Spyware, Keyloggers and etc. UnHackMe uses its own database to detect which programs you should remove from your PC. You can agree with it or not. If you find a program on the list that is OK, you can mark it as a False Positive.
- Scanning of installed programs for “Potentially Unwanted Programs” (PUPs).
- Checking for junk files, created by PUPs, adware, and spyware.
- Scanning of Windows startup programs, services, and drivers.
- Testing Windows shortcuts.
- Scanning for rootkits.
- Examining browsers search settings.
- Scanning browsers add-ons.
- Testing the hosts file and DNS settings.
- Testing startup files using several antivirus programs on Virustotal.com.
26. Sophos’s HitmanPro
[ Not Free Anymore ] HitmanPro is only 12 MB and requires no installation. It can start directly from a desktop, USB Flash Drive, CD/DVD, or a remote storage device. Even if your antivirus is being manipulated by malware or ransomware is getting a hold of your files, HitmanPro functions normally, detecting and removing the threat.
HitmanPro has the ability to remove persistent threats from within your operating system and replaces infected Windows resources with safe, original versions, all while proactively blocking reinfection attempts. A new host of malware is activated every day and can be found everywhere, even on trusted websites, evading regular antivirus programs. HitmanPro is designed to run alongside your antivirus, using its behavioral deep scanning to find and eliminate zero-day, next-gen malware that has avoided detection.
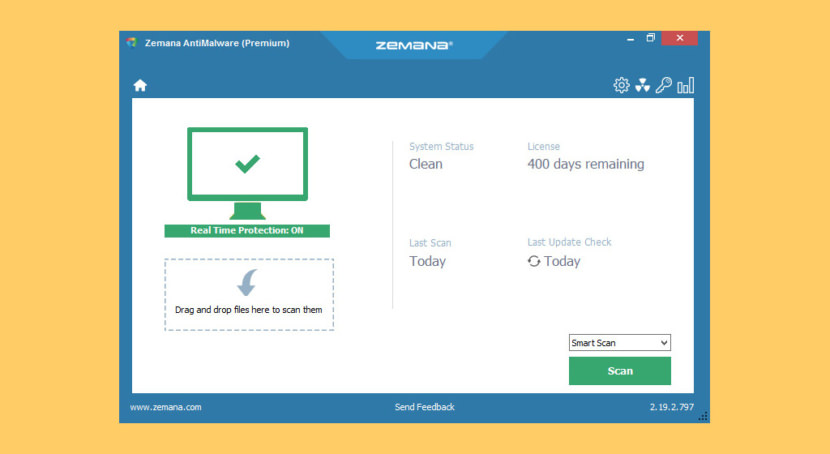
27. Zemana AntiMalware Portable
[ Not Free Anymore ] Clean your computer in minutes, no matter how badly infected! Zemana AntiMalware Free makes it possible! Zamana AntiMalware is an excellent choice to have installed on your computer, because of the low resource consumption you can use the program daily to make sure you’re not infected with any malicious files, and because of the ease to use interface the program is avaiable to every computer user and not only expert.
- Advanced Malware Detection and Removal
- Browser Cleanup
- Effective Against Rootkits and Bootkits
28. Trend Micro RootkitBuster
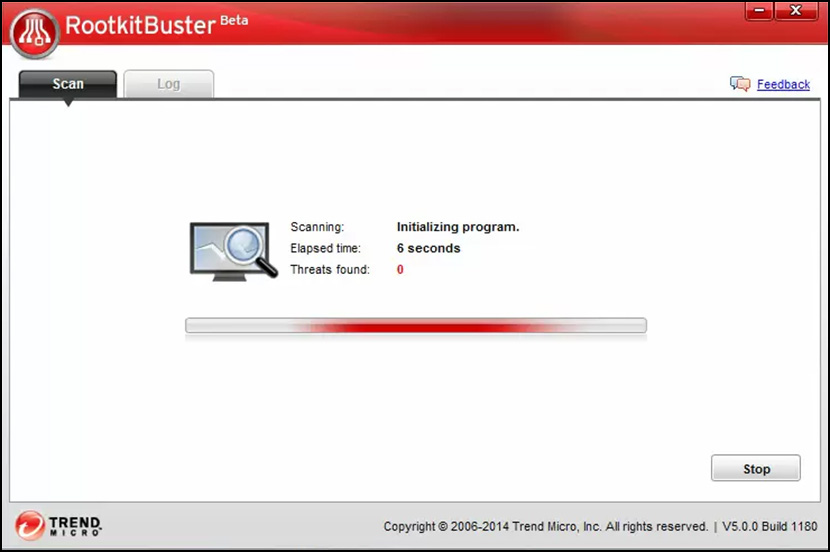
[ Discontinued ] Malicious software called rootkits can manipulate the components of the Microsoft Windows operating system to conceal how they cause harm. Rootkits can hide drivers, processes, and registry entries from tools using common system application programming interfaces (APIs). Trend Micro RootkitBuster scans hidden files, registry entries, processes, drivers, services, ports, and the master boot record (MBR) to identify and remove rootkits.
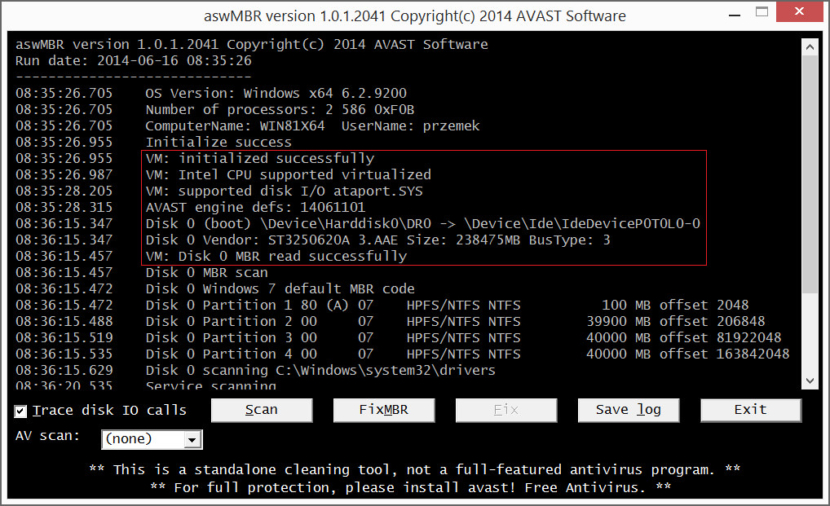
29. Avast aswMBR
[ Discontinued ] aswMBR is the rootkit scanner that scans for MBR/VBR/SRV rootkits. It can detect TDL4/3(Alureon), ZAccess, MBRoot (Sinowal), Whistler, SST, Cidox, Pihar and other malware. The current version of aswMBR uses “Virtualization Technology” to improve detection of stealth malware. Please note that to use this feature your machine & CPU must support hardware virtualization.
30. Avira PC Cleaner
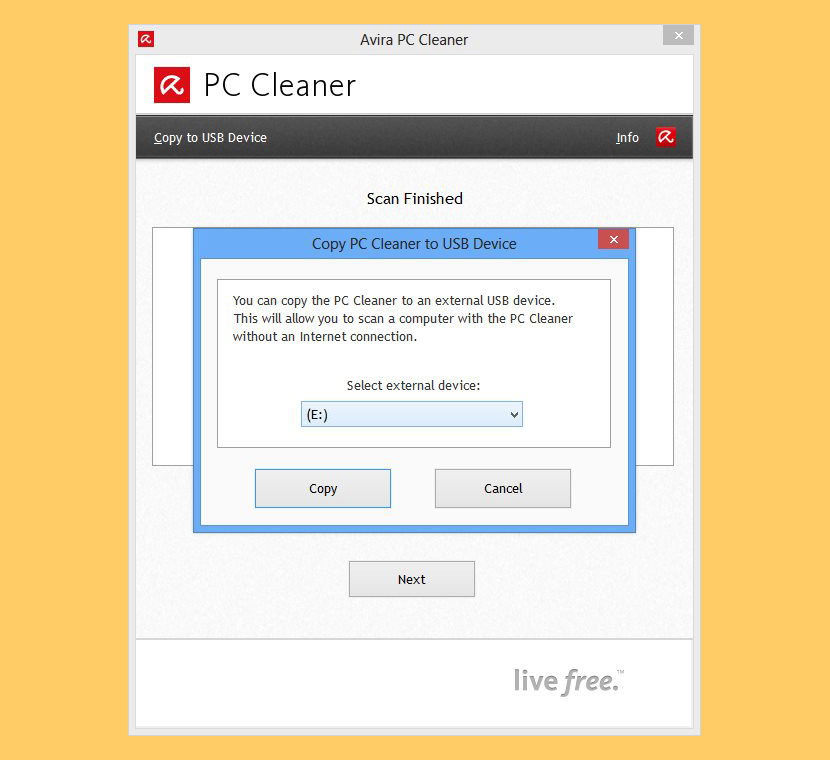
[ Discontinued ] Avira PC Cleaner is a malware scanner that works alongside other anti-malware products. It protects PCs, laptops and netbooks running Windows XP (SP3) and above. Best of all, PC Cleaner doesn’t require installation, registration or any additional drivers. On-demand scanners are often called second-opinion scanners, as they may be run next to any installed antivirus solution.
The main idea is to verify that resident security software is working correctly and that no malicious software slipped by it. While running on-demand scanners is no guarantee that the system is indeed clean, it increases the likelihood that it is.
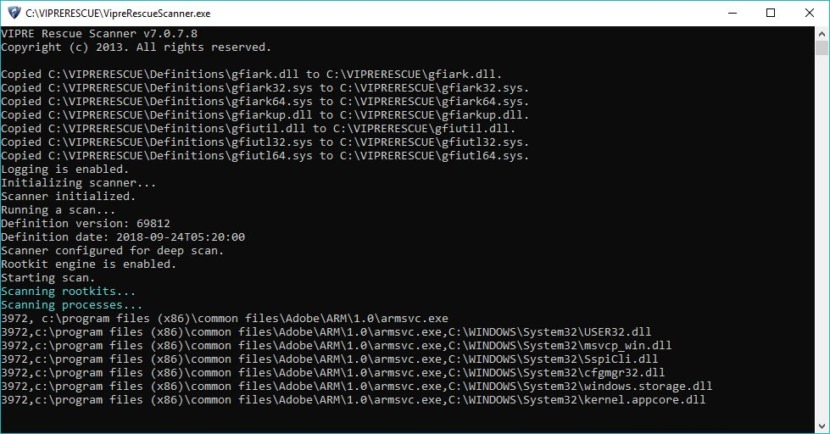
31. VIPRE Rescue
[ Discontinued ] VIPRE Rescue is a handy, easy to use tool designed to clean your computer if you are already infected with a virus and your operating system is not working properly as a result of the infection. If you are already running VIPRE and a virus has disabled it, you can still run this program to clean your computer.
32. Symantec Norton Security Scan

[ Discontinued ] The power and speed of Norton scan technology, available to you for FREE. Scans your computer and lets you know if viruses or malwares are present.
Use Norton Security Scan to determine if your system has been infected with viruses, malware, spyware, or other threats. Newly added — the Cookie Manager that you can use to check for suspicious or dangerous cookies and remove those that raise a concern.
33. BitDefender Quick Scan

[ Discontinued ] Bitdefender QuickScan uses in-the-cloud scanning technology to detect active malware on your system, in under a minute. Because it focuses on active e-threats, the product uses just a fraction of the system resources needed by a regular virus scan and requires no time-consuming virus signature updates, as the detection process is performed by remote Bitdefender servers.
34. SpyShelter Anti Keylogger
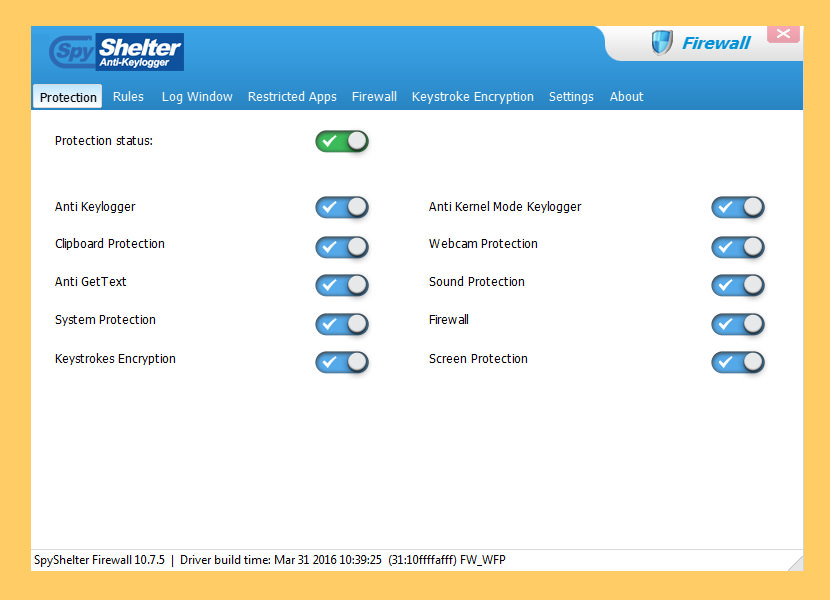
[ Discontinued ] SpyShelter Anti Keylogger provides solid protection in real time against known and unknown “zero-day” spy and monitoring software, for example: keyloggers, screen loggers, webcam loggers, and even advanced financial malware. SpyShelter Anti Keylogger monitors behavior of all currently ongoing actions on your PC and allows you to prevent any action that malware attempts to make.
Thanks to their unique technology, SpyShelter is capable of stopping both commercial and custom-made keyloggers, which cannot be detected by any anti-virus software. Since SpyShelter does not rely on any fingerprint database, you will not have to worry about zero-day malware – your registry, RAM and all applications are going to be protected from the moment you install SpyShelter.
- Protect you against stealing your private data like passwords, chat messages or credit card data.
- Detect and stop dangerous advanced zero-day malware.
- Allow you to define rules for every application. You are in charge of your PC.
- Encrypt keystrokes of all applications on kernel level.
- Protect your webcam and microphone against hijacking.
35. USEC RADIX
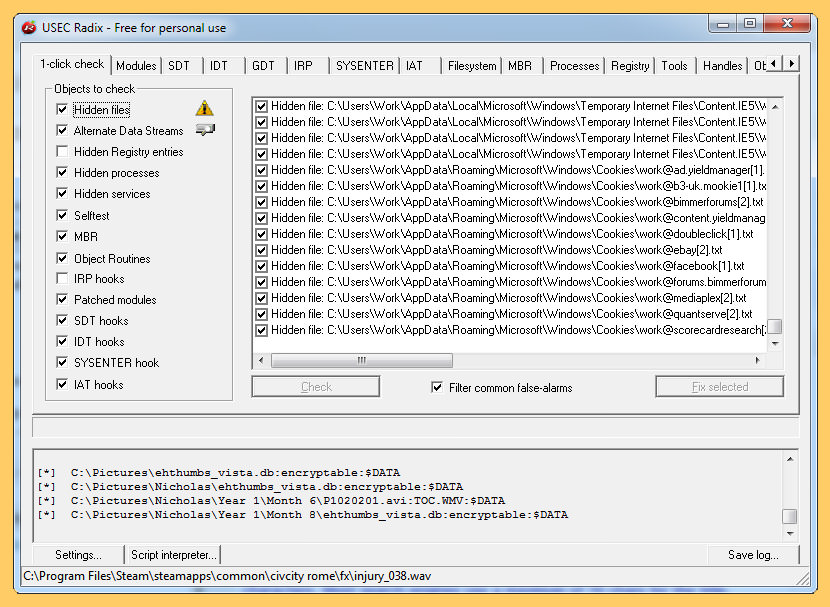
[ Discontinued ] Rootkits are dangerous programs that are downloaded from the Internet, or present in malicious purchased software, that once installed take over your computer without your knowledge. Rootkits can do anything from logging every one of your keystrokes, including usernames and passwords, email messages or even your word processing documents and sending that data off to hackers, to executing programs in the background without your knowledge or permission.
And there’s nothing that you can do about it unless you take the time right now to install Radix. It’s your best hope against combating Rootkit Attacks. Here’s what Radix does…
- Detects and removes Rootkits using sophisticated methodologies.
- Detects and repairs drivers that have been modified by Rootkits.
- Detects and repairs computer processes modified by Rootkits.
- Detects and reveals hidden processes and files, including Alternate Data Streams (ADS).
- Allows the removal of “locked” or “unremovable” processes and files.
- Provides to dump memory areas from processes.
- Shows the Global Descriptor Table (GDT) for advanced Rootkit Detection capabilities.
- Shows the Import Address Table (IAT) for advanced Rootkit Detection capabilities.
- Shows the Interrupt Descriptor Table (IDT) for advanced Rootkit Detection capabilities.
- Shows hidden Registry Keys.
- Operates in both command line mode for power users, or as a graphical tool for regular users.
36. Bitdefender Rootkit Remover
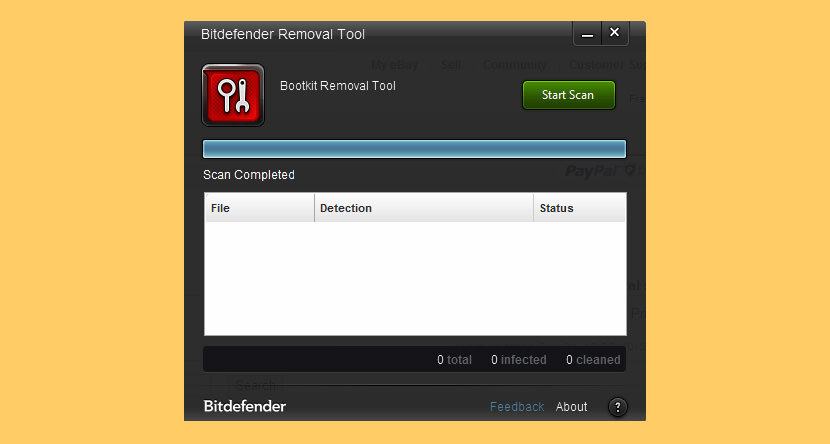
[ Discontinued ] The Bitdefender Rootkit Remover deals with known rootkits quickly and effectively making use of award-winning Bitdefender malware removal technology. Unlike other similar tools, Bitdefender Rootkit Remover can be launched immediately, without the need to reboot into safe mode first (although a reboot may be required for complete cleanup).
Rootkit Remover deals easily with Mebroot, all TDL families (TDL/SST/Pihar), Mayachok, Mybios, Plite, XPaj, Whistler, Alipop, Cpd, Fengd, Fips, Guntior, MBR Locker, Mebratix, Niwa, Ponreb, Ramnit, Stoned, Yoddos, Yurn, Zegost and also cleans infections with Necurs (the last rootkit standing). Both x86 and x64 Rootkit Remover kits are available, please choose the appropriate one for your system.
37. PCHunter anti-rootkit
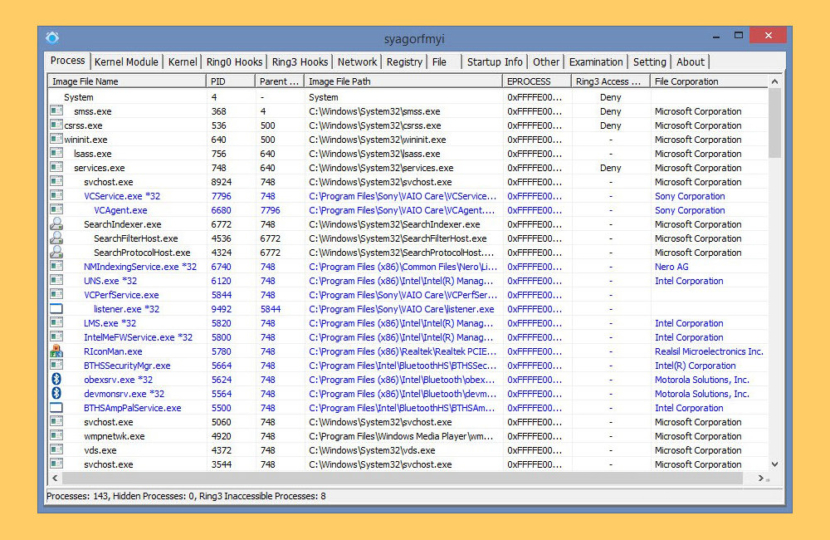
[ Discontinued ] PCHunter anti-rootkit is a free and handy toolkit for Windows with various powerful features for kernel structure viewing and manipulation. It offers you the ability with the highest privileges to detect, analyze and restore various kernel modifications and gives you a wide scope of the kernel. With its assistance, you can easily spot and neutralize malwares hidden from normal detectors.
How To Stop Viruses, Trojan and Malware
How to remove or detect a keylogger? If you suspect someone stole your password, chances are, it could be your girlfriend or boyfriend that installed a Keylogger, also known as a rootkit virus. Keyloggers are legal when used according to the law for monitoring your underage children, however, such tools can be abused for sinister use such as stealing Hotmail and Gmail password, not to mention stealing credit card information.
What is a rootkit virus? A rootkit for Windows systems is a program that penetrates into the system and intercepts the system functions ( Windows API ). It can effectively hide its presence by intercepting and modifying low-level API functions. Moreover it can hide the presence of particular processes, folders, files and registry keys. Some rootkits install their own drivers and services in the system (they also remain “invisible”).
Most anti keylogger software are designed to scramble keyboard keystrokes, they are not designed to detect and remove these keylogger software from the system, especially those keyloggers that are deeply rooted into the Microsoft Windows Root system.
More often than not, keyloggers are known as a very tough to remove spyware computer surveillance software once it is rooted into the system, sometimes they can automatically insert themselves into your antivirus’ whitelist, thus making your antivirus ignore them. You can try these alternatives.
Conclusion
Take caution when opening attachments: Keyloggers can be present in files received through email, chats, P2P networks, text messages or even social networks. If someone sends you an email out of the cold or the contents of the email are asking for your personal information, chances are there’s a keylogger in there somewhere.
How to remove rootkit virus? Where to download free rootkit detection and removal software? A rootkit virus, trojan, spyware and worm is a malware program that has administrator level access to all the network systems. What it does is it burrows itself deep into the system and hides itself, making it almost invisible and hard to be removed and detected by antivirus.
Usually rootkit malware monitor traffic, keystroke and allow backdoor access for spreading viruses and trojans, some even turn your computer into a botnet – a term known as sending out spam mail via your computer without you ever knowing.
It is hard for normal antivirus to detect their presence because rootkit tends to boot up along with windows before the antivirus is booted up. Most antivirus now comes with rootkit detector and detection ability, not to mention the ability to remove these rootkits, however, if the rootkit malware is present prior to the installation of the new antivirus, then it is not possible for the antivirus to detect it.






ClamWin Portable Screenshot ClamWin is a Free Antivirus for Microsoft Windows
Five portable antivirus and antimalware tools to carry with you at all
The article writer says they are portable, so I downloaded Kaspersky to test it.
First of all, it is NOT 700k, it is 124 MEGS.
Second, I downloaded the initial .exe to my flash drive and clicked install, then when it finally finished I discovered Kaspersky installed itself to my hard drive instead of the flash drive.
Third, it prompted my to scan my computer without downloading the updated virus signatures.
Fourth, my guess is that the author wrote this article in 1/2 hour and didn’t bother to actually download and test any of these himself, so it’s a garbage article. Does he get paid by the word and write 20 articles a day?
Hi erik, sorry for the error, when I use kaspersky Security Scan many years ago, it was portable, probably they changed the way it runs now. I updated the article and added 3 more to the list few days ago. Thanks for informing me, I will update the article.
What is the BEST portable antivirus?
There is more than likely no best. I am about to partition a flash USB drive and install all of these if i can. The next time i suffer an infection, i will just run through as many as i can.
no need to partition – create folders when inserted and install 2-3 on a flash drive.
As for me, it is GridinSoft Trojan Killer Portable
TrustPort Antivirus USB Edition (Portable), Download now!!!
F-Secure On Line Scanner
+
SophosVirusRemovalTool
This is a cookie cutter list of garbage! McAfee? …and Norton? Really??
It’s no wonder these generic “help/info” sites that push big Corp. crap come up 1st in search engines. lol.
The three best portable malware scanners not even listed : 1) Zemana anti malware portable (free) uses several anti virus engines eg Bitdefender and Kaspersky , its very fast & powerful cloud AM
(2) Emsisoft Emergency Kit doesnt need internet connexion (free) (3) Hitman Pro also uses multiple engines including Bitdefender , free for first use
Thanks for the info. Zemana and Hitman are freemium, thus not in the list but I think it is worth including. I’ll include all 3 when I update the article.
Thanks but Zemana portable free – (Zemana.AntiMalware.Portable.exe) is a recent introduction which is permanently free and not a trial version. It is different to the trial Premium version you show. It is a completely portable cloud version which I use all the time from a usb stick to check for pc infections.
Comodo requires a reboot – can’t use on servers.
Comodo Cleaning Essentials doesn’t. Tested on Windows Server 2020 R8 x64
a typo -> R2
Microsoft Safety Scanner is NOT Portable….
Avira also installed on the hard and superseded and disabled windows defender. I agree with erik that the author didn’t actually test these programs. Incidentally Trend Micro Housecall doesn’t install and it is not even mentioned. I definitely don’t want any of them to install either and both Kaspersky and Avira did indeed install. I gave up after the second. This list is inaccurate if you want to use AVs that don’t install.
Thank you very much… Had a few Problems in my Registry and no antivirus was working.
Also i couldnt install a new one… But this gives me hope..
Thanks for the list
Glary utilities portable to fix the registry errors? It also comes with a worthwhile (though vastly inferior) anti-malware. Though it sounds like you might be in need of a repair disk if your system is that damaged. Kaspersky seems to have one of the best on the market right now but I personally prefer Avira or Avast for rescue disks as Kaspersky has issues on USB.
Emsisoft has begun to play dirty with non-configurable pop-up ad that always appears whenever the application closes. After more than 10 years in existence, what was a wonderful free backup scanning solution turned into a monstrosity.
This is totally incorrect…
i only use antivirus apps that work alongside other anti-malware apps, kapersky and so many others want to own our systems so they don’t get my approval
Hello, and firstly thank you for the information; it is what I was l looking for.
Just have to alert you to Comodo not being free. There is a free version available for phones though. Not to worry, I’ll blast that little asswiggling insect with the other 22 that are hopefully available, and if that doesn’t work, I’ll just pour cough syrup over the machine and call it a day. Thnx again.
Symantec Norton Power Eraser seems to be the best as it can also erase some files, but Dr.Web CureIt is not good as it don’t catches anything in my experience.
Avira dose not support Vista – says so when I try to download it
I’m surprised DoesNotBelong by Furtivex wasn’t mentioned. Has saved me a few times now bc I download a lot of torrents lol