As a kid, we’ve all been there and done that – that is downloading pirated software from torrent sites with cracks, be it antivirus, games or Microsoft Office software. Little did they know, hackers knew the reason you download an antivirus program is because you do not have a security software installed therefore you are vulnerable, and the best way to infect your Windows computer is to include a ‘disabled’ antivirus with a trojan horse.
Related Article 😍💰👉 5 Free Antivirus With 60+ Multi-Engines – The Best Antivirus Protection
Comodo Leak Tests used to be a very reliable and popular penetration test tool, but unfortunately, they’ve decided to discontinue the product. Even if you decide to come clean and purchase a genuine antivirus, sometimes it might be too late, this is because the virus is integrated into your system that will disable all new antivirus during installation, rendering them useless while you think you are well protected. One way to find out if your antivirus is working is to simulate an actual ‘harmless’ virus attack.
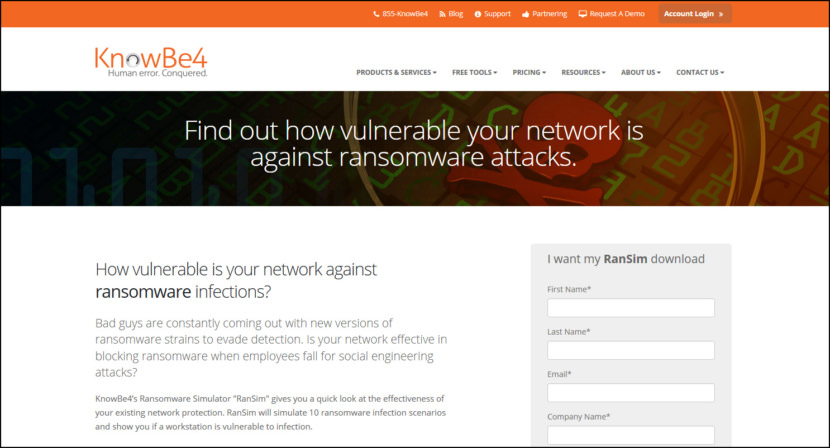
1. RanSim
Free Ransomware Simulator Tool
How vulnerable is your network against ransomware attacks? Bad guys are constantly coming out with new versions of ransomware strains to evade detection. Is your network effective in blocking ransomware when employees fall for social engineering attacks?
KnowBe4’s Ransomware Simulator “RanSim” gives you a quick look at the effectiveness of your existing network protection. RanSim will simulate 10 ransomware infection scenarios and show you if a workstation is vulnerable to infection.
- 100% harmless simulation of a real ransomware infection
- Does not use any of your own files
- Tests 10 types of infection scenarios
- Just download the install and run it
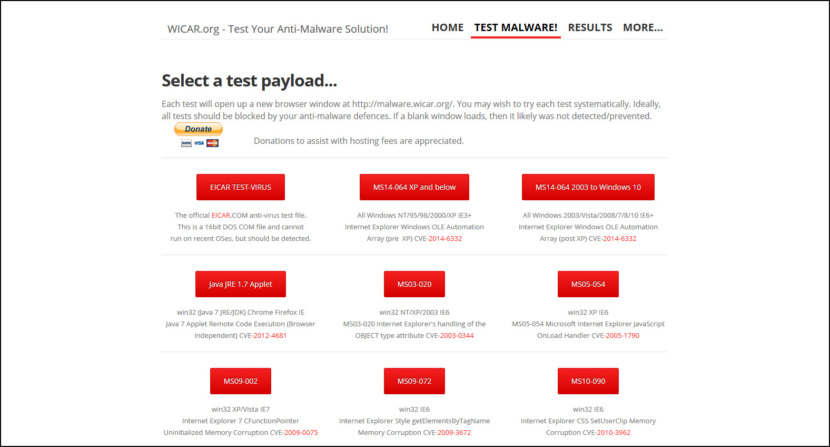
2. WICAR
Test Browser Security
The wicar.org website was designed to test the correct operation of your anti-virus / anti-malware software. The name “WICAR” is derived from the industry standard EICAR anti-virus test file, which is a non-dangerous file that all antivirus products flag as a real virus and quarantine or act upon as such.
By being able to execute a test virus program safely, the end user or network administrator can ensure that the anti-virus software is correctly operating (without utilising a real virus which may damage the system should the anti-virus software fail to function).
The Test Malware! page contains widely abused browser exploits you may safely click on, to test your defences. Donations to assist with the operational and hosting costs are welcome.
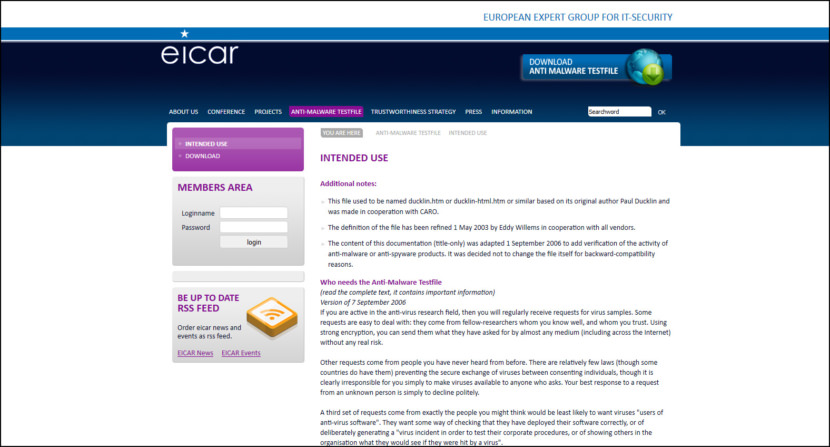
3. EICAR
Simple Antivirus Test
This test file has been provided to EICAR for distribution as the “EICAR Standard Antivirus Test File”, and it satisfies all the criteria listed above. It is safe to pass around, because it is not a virus, and does not include any fragments of viral code. Most products react to it as if it were a virus (though they typically report it with an obvious name, such as “EICAR-AV-Test”).
4. FortiGuard
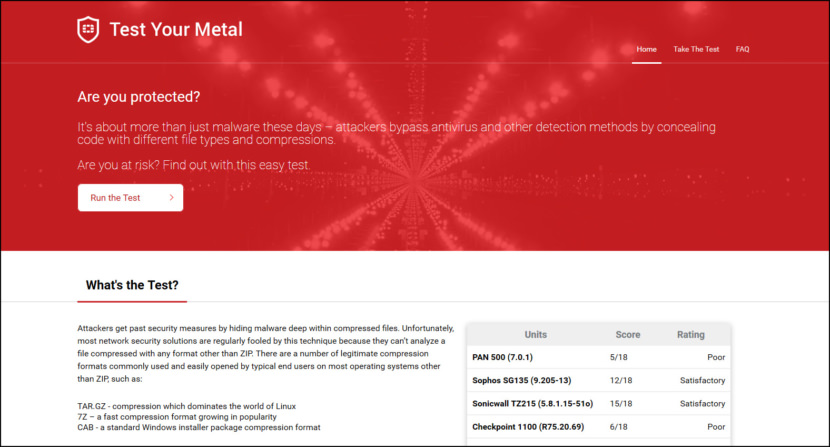
Test Downloadable Zip Compression
Are you protected? It’s about more than just malware these days – attackers bypass antivirus and other detection methods by concealing code with different file types and compressions. Are you at risk? Find out with this easy test. Attackers get past security measures by hiding malware deep within compressed files.
Unfortunately, most network security solutions are regularly fooled by this technique because they can’t analyze a file compressed with any format other than ZIP. There are a number of legitimate compression formats commonly used and easily opened by typical end users on most operating systems other than ZIP, such as:
- TAR.GZ – compression which dominates the world of Linux
- 7Z – a fast compression format growing in popularity
- CAB – a standard Windows installer package compression format
5. IKARUS Security
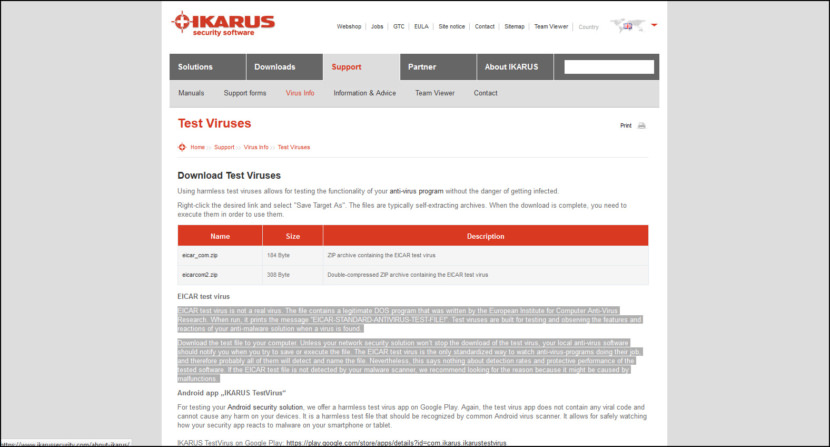
Downloadable EICAR Test Files
EICAR test virus is not a real virus. The file contains a legitimate DOS program that was written by the European Institute for Computer Anti-Virus Research. When run, it prints the message “EICAR-STANDARD-ANTIVIRUS-TEST-FILE!”. Test viruses are built for testing and observing the features and reactions of your anti-malware solution when a virus is found.
Download the test file to your computer. Unless your network security solution won’t stop the download of the test virus, your local anti-virus software should notify you when you try to save or execute the file. The EICAR test virus is the only standardized way to watch anti-virus-programs doing their job, and therefore probably all of them will detect and name the file.
Nevertheless, this says nothing about detection rates and protective performance of the tested software. If the EICAR test file is not detected by your malware scanner, they recommend looking for the reason because it might be caused by malfunctions.
6. ShieldUp
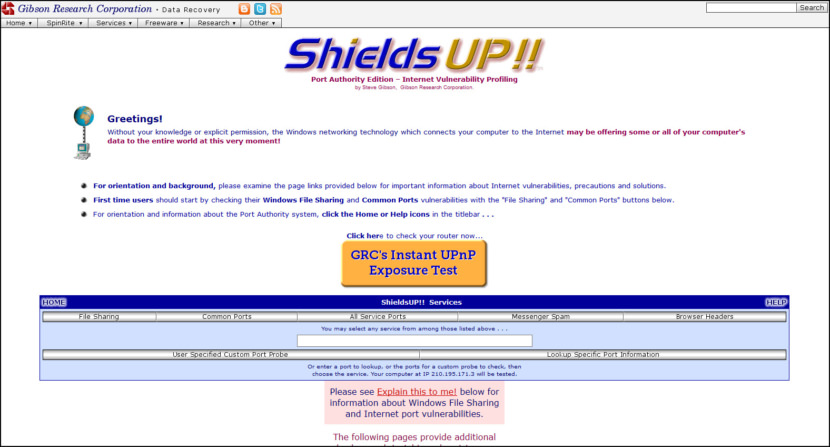
Test Windows DNS & Router UPnP Exposure
Without your knowledge or explicit permission, the Windows networking technology which connects your computer to the Internet may be offering some or all of your computer’s data to the entire world at this very moment! Many Internet connection IP addresses are associated with a DNS machine name. (But yours is not.)
The presence of “Reverse DNS”, which allows the machine name to be retrieved from the IP address, can represent a privacy and possible security concern for Internet consumers since it may uniquely and persistently identify your Internet account — and therefore you — and may disclose other information, such as your geographic location.
7. SpyShelter Security Test Tool
Test Windows Security
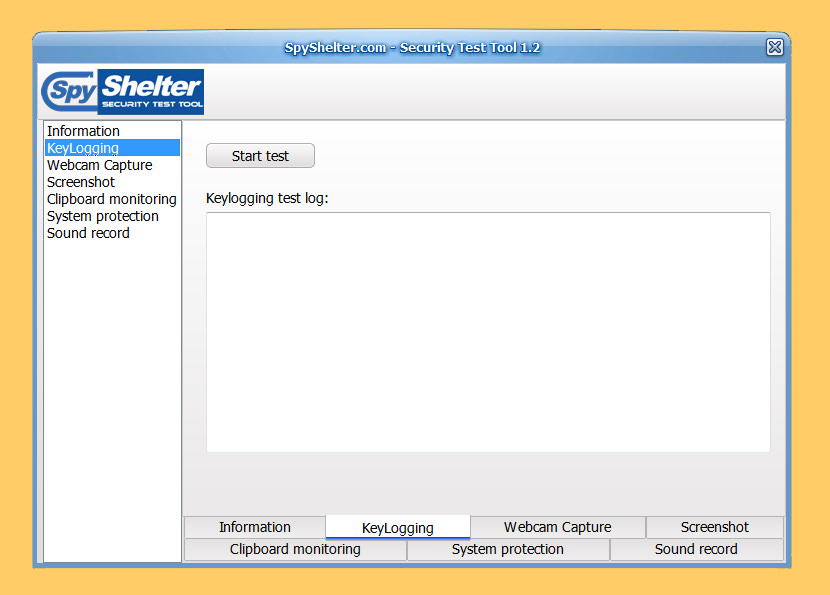
[ Discontinued ] Security Test Tool presented on this page is a non-malicious application which can be used on live systems. It does not require installation. This tool simulates a few methods used by sophisticated malware to steal your data. It will not damage your system files, and all captured data is stored locally on your PC until the moment you close the application. Test your security software and find out if it protects you against information-stealing malware. This Security Test Tool consists of 6 separate modules:
- Keylogging test
- Webcam capturing test
- Test Keystroke Encryption
- Screen capturing test
- Clipboard capturing test
- Sound recording test
- System protection test (Registry access, writing file to startup folder, service registering)
8. TESTmyAV
Test Ransomware & Malware
[ Discontinued ] This site contains 100+ real malicious and extremely damaging malware. Get your hands on fresh malware for testing your antivirus software and maybe mutate it yourself with a packer. On TestMyAV.com they’ve got plenty of malware for you to use in your testing. Just go to the malware page and start there.
You can also source malware from many other places on the Internet and from your local email spam folders. Whatever you use, you’ll need to handle it carefully to make sure you don’t accidentally infect a machine or let it be scanned prematurely before you’ve started the proper testing.



![Download ESET Endpoint Antivirus For Business [ Best Security Protection ]](https://cdn3.geckoandfly.com/wp-content/uploads/2018/03/530-eset-logo-150x150.jpg)

anovanetlabs have a tool to test your firewalls ability to block files compressed in different ways. Free to use and they email out out the results.
Avast Total Security Stopped every single one