Category: Computer and Internet Security
Can you make money hacking a server? The answer is yes. Why waste your talent on destroying when it can be used to create a better life for yourself. Be a bug bounty hunter and earn more than $350,000 yearly. Bug bounty programs award hackers an average of $50,000 a month, with some paying out $1,000,000 a year in total.
Related Article 😍💰👉 5 Free Linux OS For Penetration Testing, IT Security Assessments And Network Vulnerabilities
Tommy DeVoss used to break into websites illicitly. But after serving time for his crimes, he now uses his skills to earn an honest living. Through arrangements known as bug bounty programs, companies pay him to find security holes in their systems. He’s now earned more than $1 million in this emerging profession. This is an episode of Next Jobs, a mini-documentary series about careers of the future hosted by Bloomberg Technology’s Aki Ito.
A bug bounty is a reward that is paid out to developers who find critical flaws in software. Usually a company will put up their software or server for a test, they allow you to comb through the code of an application and look for flaws, depending on the security bug, rewards can vary. Be a hacker now!
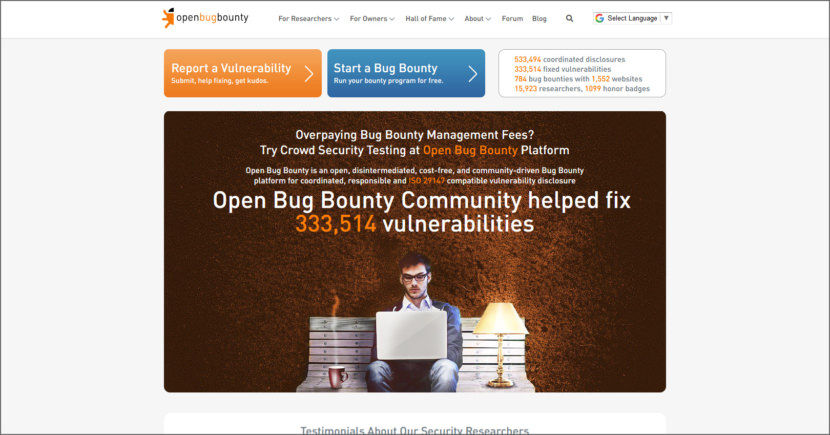
1. Open Bug Bounty
Started by a group of independent security researchers in 2014, Open Bug Bounty is a non-profit platform designed to connect security researchers and website owners in a transparent, respectful and mutually valuable manner. Their purpose is to make the Web a safer place for everyone’s benefit.
Open Bug Bounty allows any verified website owners to run a bug bounty for their websites at no cost. The purpose of this non-profit activity is to make relations between website owners and security researchers sustainable and mutually beneficial in a long-term perspective.
2. Synack
Comprehensive penetration testing with actionable results. Continuous security scaled by the world’s most skilled ethical hackers and AI technology.
- Built by hackers for hackers – Become one of the select few SRT members and hack among the best in the world, sharpening your skills and putting them to the test.
- Hydra technology assistance – Hydra is an intelligent AI scanning tool that alerts their SRT members of possible vulnerabilities, changes, or events.
- Guaranteed income through Missions – In addition to bounties for finding vulnerabilities, Missions provide payment for methodology-based security checks.
3. hackerone
Hacking is here for good, for the good of all of us. More Fortune 500 and Forbes Global 1,000 companies trust HackerOne to test and secure the applications they depend on to run their business. Join us for a discussion on vulnerability disclosure policies (VDPs) and why they are top of mind following the issuance of a draft Binding Operational Directive (BOD) 20-01 by the U.S. Department of Homeland Security’s Cybersecurity and Infrastructure Security Agency.
- Establish a compliant process for receiving and acting on vulnerabilities discovered by third-parties – Ensure bugs found by security researchers, ethical hackers, or other external parties reach the right people in your organization.
- Improve your Pen Test results with a project-based vulnerability assessment program – Capture the intelligence of their trusted community in a time-bound program that consistently outperforms traditional penetration testing.
- Launch a private, fully-managed bug bounty program for continuous coverage – Take a proactive approach to finding critical vulnerabilities across your critical surfaces with the full support of HackerOne’s security experts.
4. bugcrowd
Bugcrowd reduces risk with coverage powered by their crowdsourced cybersecurity platform. Go beyond vulnerability scanners and penetration tests with trusted security expertise that scales — and find critical issues faster.
- 10x Better Results – Continuous coverage surfaces more critical vulnerabilities
- Secure from the Start – Automated workflows and remediation advice empower DevOps
- Right Team Every Time – Advanced analytics connect the right security skills to every project
- Fast Find, Fast Fix – Expert triage processes validate faster and ensure 95% signal to noise
- Contextual Intelligence – Program performance and industry benchmarking demonstrate ROI
- Creativity at Scale – Global crowd of trusted hackers to stay a step ahead of adversaries




alert(“Your website is vulnerable to XSS attack, fix it”)