How to uninstall Kaspersky Antivirus? It is important that any previously installed antivirus software is uninstalled from your Windows system before installing another new or different security software. Typical uninstallation via the Microsoft Windows removal tool (Add/Remove Programs) often does the job, However there are times when you may experience issues using the normal method and these official tools below will assist you.
Related Article 😍💰👉 4 Unlock And Recover Hard Drive Password Removal Tool
How to remove, reset or recover your forgotten laptop BIOS password? There are many methods, each method has its own strength and weakness. If you forgot your BIOS password, chances are you don’t have access to your computer, not even in Safe Mode, therefore making this software useless. For Desktop users, removing the battery for 5 minutes will reset the BIOS whereas laptop users might not have the option without invalidating the warranty of the laptop, this is where software comes in handy.
On laptops, more often than not the password is usually stored in an eeprom on the motherboard and not in the cmos. You need an eeprom programmer/eeprom reader (electronic device) to retrieve the password. If you erase the cmos (ie. cmospwd /k) and if the password is really stored in an eeprom, you won’t be able to boot anymore. You can get/buy eeprom programmers in electronic shops or labs, you need another PC to use it. You can desolder the eeprom with hot air or you can try to “clip” the eeprom. With the eeprom programmer, backup your eeprom and run cmospwd /d /l eeprom_backup. If you don’t see the password, you can try to fill the eeprom with zero or FF, don’t forget to reset the cmos.
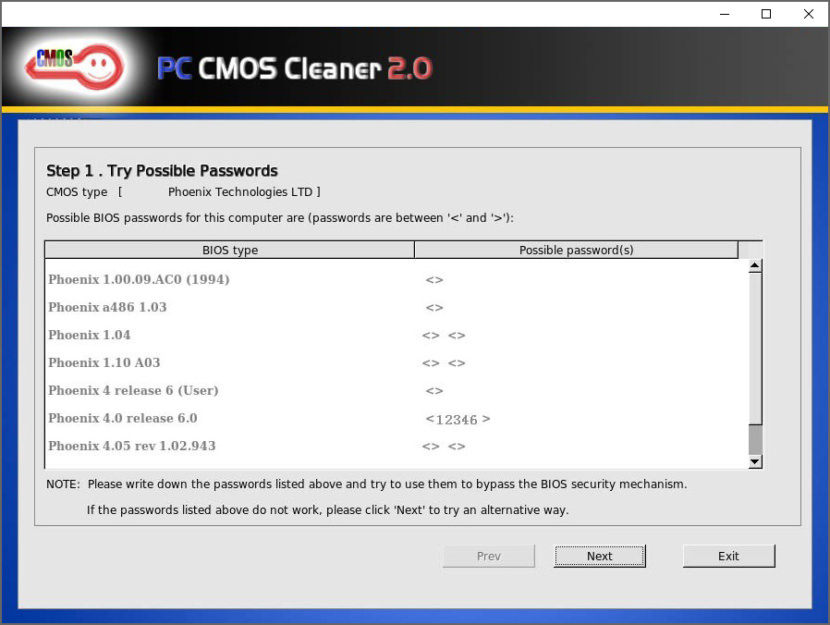
1. PC CMOS Cleaner
PC CMOS Cleaner is an easy-to-use tool to recover, delete, decode and display the superior passwords stored in BIOS whatever the brand is. Most types of BIOS are supported. It’s a bootable CD that runs on x86 and x86_64 computers. No need to pay expensive fees to experts. It’s a useful tool for users to get their lost BIOS password back, or clean passwords from an old computer bought from others.
- Support all x86, x86_64 Personal Computers.
- Support most BIOS, such as: AWARD, AMI, Compaq, Phoenix, Samsung, IBM, Compaq, DTK, Thinkpad, Sony, Toshiba and so on.
- Display the superior passwords of the BIOS .
- Remove BIOS password(will set the BIOS to default status, need reset date).
- Set the BIOS to default state
2. CMOS De-Animator 3
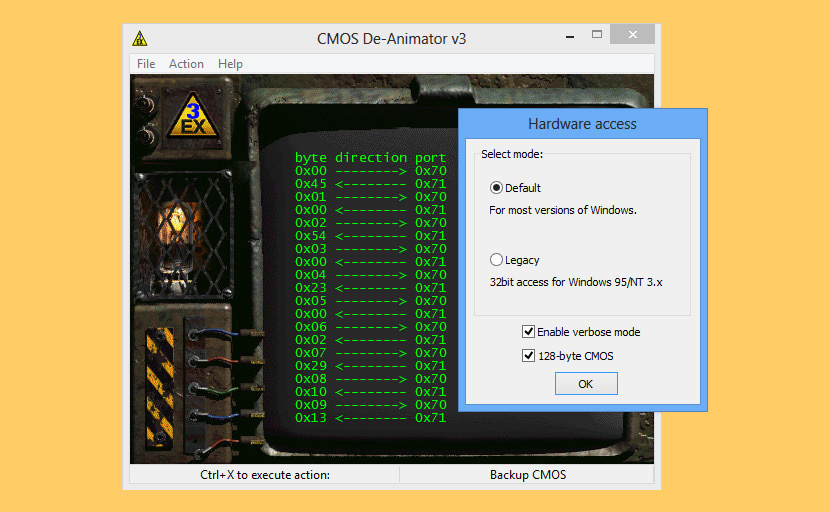
CMOS De-Animator is a service utility for your system’s CMOS RAM. Unlike its predecessor, the CMOS De-Animator 2.0, the new version includes a graphical interface and CMOS-backup options along with the “Clear CMOS” procedure, which was the original version’s only purpose. So, you can now backup the main CMOS settings to a file, or restore them later. The application supports all 32-bit and 64-bit Windows operating systems except Windows 95 and Windows NT 3.51; for these old systems, you have to use De-Animator’s previous version.
Compared with CMOS De-Animator v2, the new features include an interactive GUI, command-line support with optional silent (unattended operation) switch, log file generation, and experimental EEPROM / low level BIOS reading support! Original features – backup, restore and reset the CMOS RAM – of the old De-Animator are, of course, intact and still conveniently accessible. The same goes for extreme backward compatibility, just as with previous versions – the application runs on a Windows NT 3.51 just as fine as under Windows 8, 32-bit or 64-bit!
3. CmosPwd
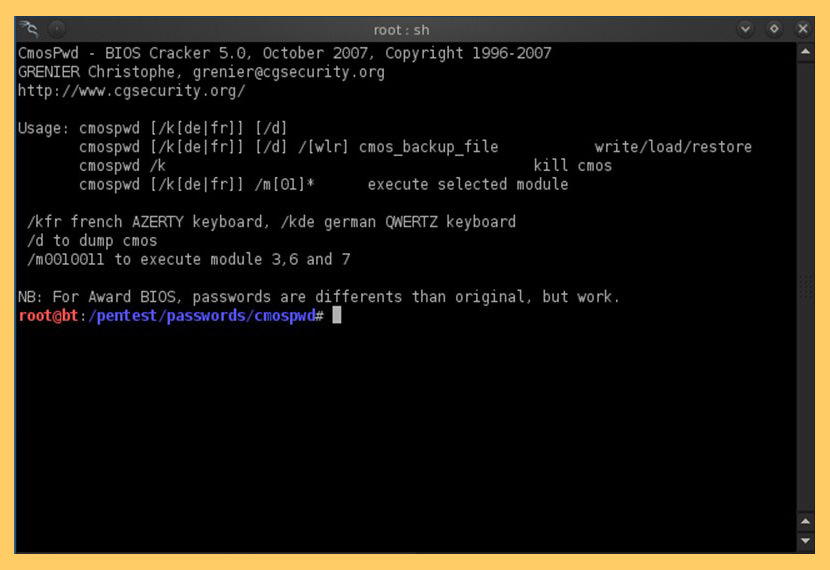
CmosPwd decrypts password stored in cmos used to access BIOS SETUP. The software is also able to save the configuration of a BIOS, which protects the data by duplicating and storing it in a secure location on the hard disk. With CmosPwd, you can also backup, restore and erase/kill cmos. CmosPwd is free, it’s distributed under Open Source GPL. Works with the following BIOSes
- ACER/IBM BIOS
- AMI BIOS
- AMI WinBIOS 2.5
- Award 4.5x/4.6x/6.0
- Compaq (1992)
- Compaq (New version)
- IBM (PS/2, Activa, Thinkpad)
- Packard Bell
- Phoenix 1.00.09.AC0 (1994), a486 1.03, 1.04, 1.10 A03, 4.05 rev 1.02.943, 4.06 rev 1.13.1107
- Phoenix 4 release 6 (User)
- Gateway Solo – Phoenix 4.0 release 6
- Toshiba
- Zenith AMI
4. !Bios
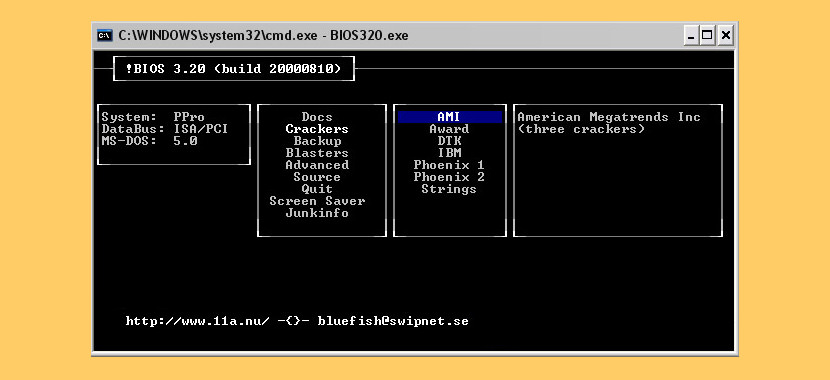
!Bios ( a very old program, might work on older computers ) is a tool originally developed for a brute, blunt removal of passwords from BIOSes. Through its development it has been severely extended, and Eleventh Alliance have now received emails from computer support divisions, hackers and not least of all ordinary computer users who have expressed gratitude for what they consider one of the best toolkits available.
- !Bios can decrypt the passwords used in some most common BIOS (including various bioses/versions by IBM, American Megatrends Inc, Award and Phoenix).
- !Bios can also save and restore the IBM standard CMOS/NVRAM memory where almost all common Bioses store the BIOS setup settings.
- !Bios can save the part of the RAM dedicated for the BIOS (which has security implications in some BIOSes as encryption algorithms and/or password may actually reside here in some badly coded BIOSes).
- !Bios can do crude, brutal attacks (“blasters”) which remove passwords from a lot of Bioses. A bit dangerous though, can give unexpected and unwanted results.
- !Bios has a CMOS editor where through an interface with similarities to several hex-editors can modify the CMOS/NVRAM memory in binary, decimal and hexadecimal ways. (only advised for very experienced hackers)
- !Bios has a command line interface (CLI) and a very simple VGA-text interface, GUI. If no parameters is passed to !Bios, it starts the easy-to-use GUI, otherwise it starts the GUI.
- !Bios has built-in support pages which provides several tricks and tips, notes about known backdoors etc.
5. Clear CMOS Jumper or Dipswitch Settings
There’s a jumper on your motherboard that you’ll need to identify and remove. Most motherboards make your job easier by actually labeling the correct jumper as “BIOS config” or something similar. Remove the jumper, and then turn the computer on. In some cases, you will have to remove the jumper while the system is powered up, though to minimize risk, try doing this first with the computer off. In today’s quick tip I show off the quick and easy process of resetting the CMOS on your computer. Simply move the CMOS jumper to the last 2 pins for about 5-10 seconds depending on your motherboard, and then replace it back to its original position.
6. Remove Internal CMOS Battery

For desktop users, open up your computer casing and look for the battery. Remove the battery for approximately 5 minutes (maybe longer, depending on the motherboard) and slot it back. By removing the battery and depriving the motherboard’s flash memory of power supply, you are essentially resetting the settings back to default when the existing data in BIOS are cleared. This method works well for desktop, however this is not practical for laptop users unless the warranty expired a long time ago. This method might or not not work, it depends on the type of motherboard.
7. BIOS Password Generator For Laptops
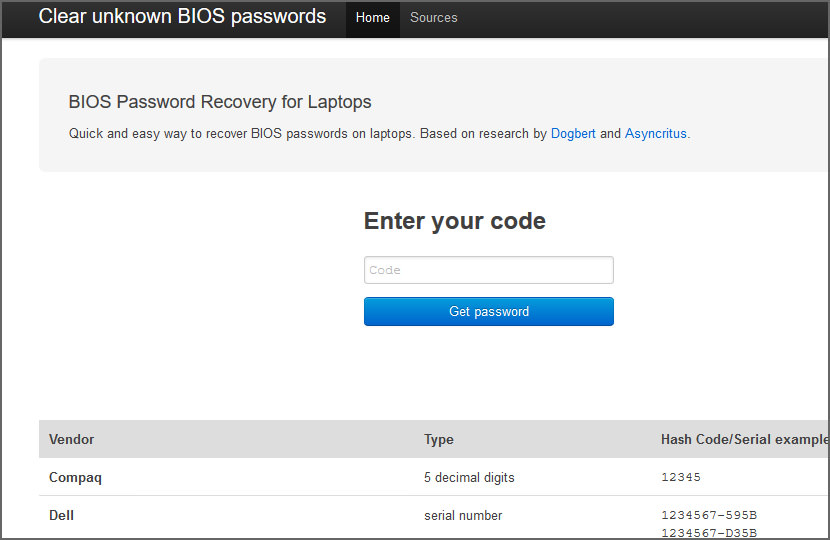
How to Reset a Dell laptop BIOS Password? Quick and easy way to recover BIOS passwords on laptops, this site contains master password generators for various BIOS/UEFI firmware. Based on research by Dogbert and Asyncritus. When a laptop is locked with a password, a checksum of that password is stored to a so-called FlashROM – this is a chip on the mainboard of the device which also contains the BIOS code and other settings, e.g. memory timings. For most brands, this checksum is displayed after entering an invalid password for the third time.
The dramatic ‘System Disabled’ message is just scare tactics: when you remove all power from the laptop and reboot it, it will work just as before. From such a checksum (also called “hash”), valid passwords can be found by means of brute-forcing.
8. Using MS DOS Command
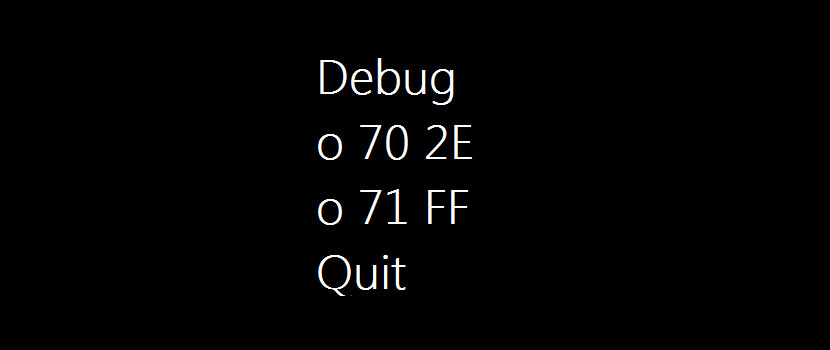
This method works if you have access to Windows because this method requires MS DOS. Open Command Prompt from Programs menu and provide following commands:
- debug
o 70 2E
o 71 FF
quit
Important – The first character in the above commands is English alphabet “o” and not the number 0. Now, after providing the above commands in MS DOS, restart your system and it should automatically reset the CMOS Settings along with the BIOS password. How does it work? In this “MS DOS Debug Command” method, the “o” character present at first in these commands, outputs the values to IO ports. The number 70 and 71 are port numbers which are used to access CMOS memory. By providing FF value they are telling CMOS that there is an invalid checksum and it resets the CMOS settings as well as BIOS password.
9. Backdoor Password By Manufacturer
Some BIOS manufacturers or the laptop maker put a backdoor password in BIOS and will always work regardless of what password you have set in the BIOS. It is a master password which is used for testing and troubleshooting purposes, or in the event you lock yourself out of your own laptop.
AMI BIOS Passwords:
- A.M.I.
AAAMMMIII
AMI?SW
AMI_SW
AMI
BIOS
CONDO
HEWITT RAND
LKWPETER
MI
Oder
PASSWORD
AWARD BIOS Passwords:
- 01322222
589589
589721
595595
598598
ALFAROME
ALLy
aLLy
aLLY
ALLY
aPAf
_award
award
AWARD_SW
AWARD?SW
AWARD SW
AWARD PW
AWKWARD
awkward
BIOSTAR
CONCAT
CONDO
Condo
d8on
djonet
HLT
J64
J256
J262
j332
j322
KDD
Lkwpeter
LKWPETER
PINT
pint
SER
SKY_FOX
SYXZ
syxz
shift + syxz
TTPTHA
ZAAADA
ZBAAACA
ZJAAADC
PHOENIX BIOS Passwords:
- BIOS
CMOS
phoenix
PHOENIX
Misc Common Passwords:
- ALFAROME
BIOSTAR
biostar
biosstar
CMOS
cmos
LKWPETER
lkwpeter
setup
SETUP
Syxz
Wodj
Other Manufacturer BIOS Passwords:
- Biostar – Biostar
Compaq – Compaq
Dell – Dell
Enox – xo11nE
Epox – central
Freetech – Posterie
IWill – iwill
Jetway – spooml
Packard Bell – bell9
QDI – QDI
Siemens – SKY_FOX
TMC – BIGO
Toshiba – Toshiba
VOBIS & IBM – merlin
Note
The BIOS is the basic instruction set that “teaches” the computer how to access its media. If the BIOS is password protected, the computer will not function without the password. BIOS passwords are used in two ways: To prevent modification of the BIOS settings and to completely stop the computer from booting.
If you’ve got crucial data on your system, need it urgently, and can’t get past the BIOS. Remember that you can always remove the hard drive with the data and access it from another system. The BIOS password (typically) only pertains to the motherboard. There are some manufacturers, IBM and Dell included, who are encrypting the HDD to the motherboard. If this is the case, try contacting the manufacturer for a password to unlock the HDD.






This information is intended for experienced users. It is not intended for basic users, hackers, or computer thieves. Please do not try any of following procedures if you are not familiar with computer hardware. I’ll not be responsible for the use or misuse of this information, including personal injury, loss of data or hardware damage. So use it at your own risk.
A. By Using the Motherboard Jumper:
In most motherboards CMOS battery is soldered, which makes it difficult to remove the battery. In this case we use another method.
Almost all motherboards contain a jumper that can clear all CMOS settings along with the BIOS password. The location of this jumper varies depending upon the motherboard brand. You should read your motherboard manual to check its location. If you don’t have the manual then look for the jumpers near the CMOS battery. Most of the manufacturer label the jumper as CLR, CLEAR, CLEAR CMOS, etc.
When you find the jumper, look carefully. There will be 3 pins and the jumper will be joining the center pin to either left or right pin. What you need to do, is remove the jumper and join the center pin to the opposite pin. e.g. if the jumper joins center pin to left pin, then remove it and join center pin to right pin. Now wait for a few seconds and then again remove the jumper and join the center pin to left pin.
Make sure to turn the PC off before opening the cabinet and resetting the jumper.
B. By Using Software:
I have found that BIOS/CMOS Password Recovery Tool is the most effective.:
BIOS/CMOS Password Recovery Tool is a program that works instantly to remove any lost or forgotten BIOS/CMOS password. Simply boot your PC to DOS and execute the program, and get access to forgotten BIOS/CMOS passwords in just seconds
Thanks for the info
BIOS/CMOS Password Recovery Tool Service
Hai am loocking for bios password removerl at newcity computers repairs ineed help for removing acer laptop password plz by infomation or cracks
i need the bios password of dell inspiron N5030
I have tried everything and still I get need administrator password
Hi please help I has an Asus model g73s and I forgot my startup bios password and removing the battery didn’t work. Is the any other way I can be able to unlock my laptop. Please help.
I need to break dell laptop bios password thanks
You can get your Acer bios master password here. They also do this for Dell, HP/Compaq and Fujitsu-Siemens,, Advent, ASUS, Gateway, Samsung and Sony
The Master Password will delete all Bios passwords giving you access to your locked computer again.
hi,sorry for my english,I HAVE a notebook Asus pro 76 s,and i forgot bios parole.can you help me somehow,please.I put out the bios baterry but nothing.please help me .thank you very much.
HELP!! No display on monitor after bios reset!
I need the bios of computer Dell 3340
Bios password for Lenovo
Dell latitude D630 wants bios password
I need the bios of Hp Pro book 6570b computer
Bios ver. 68ICF v. F.68
i want to dell latitude bios password recovery tools
have you found it?
sorry i have laptop of acer sorry may you help me the master password to resetting of bios version phoenix technologies LTD V1.32,2/1/2008
Bios password in b460e
plase i need a pasword bios for asus x58c
please give me a master password for acer travelmate tmp455-mg .. I forget my bios password .. please help me
Do these methods work for the Acer Swift 1?I have one and for months I have tried everything and nothing anyone knows what I could do?
If i have the software, how do i boot because first thing the computer says ENTER PASSWORD.
I have the CD in my Cd rom, but i cant boot from it because the PASSWORD PROMPT comes before booting.
Pls help. Whatsapp +26876820441
i am trying to change acer laptop bios password you have posted i can get master password here i have search site but cannot locate said password can you forward it to me thx sean
Hi, I’m using acer swift 3 SF315-51G. Few days ago i’ve update my bios from v1.03 to v1.06. After then when i’m trying to open boot menu it is asking me password, but i’ve never given any password. Bios failure code 1901346771. Please help me to get out of this problem.
hi
i have my laptop asus i want to remove bios password what can i do now
give me best answer the model number is ASUS A8J.
PLS HELP ME
i have ASUS A52J SERIES COREI3 THAT HAVE BOARD PASSWORD HOW CAN I REMOVE IT.
You need to break the password. You visit the website
– Unlock password bios Dell
– Unlock password bios Asus
– Unlock password bios Acer
– Unlock password HP-Compaq
– Unlock password bios Sony
– Unlock password bios Samsung
– Unlock password bios Gateway
– Clear password bios Phoenix
– Remove password bios Fujitsu
password bios. Acer 8572t
How To Clear CMOS (Reset BIOS)?
how to clear my toshiba satellite r830-143 bios passsword plesse reply verry ajend
Have you tried contacting Toshiba? Usually they have a master key if the following master key doesn’t work. Another method is to remove the laptop battery and the internal tiny battery. This will reset the Bios and remove the password, but it might damage the laptop or void the warranty.
Acer e5-571-34LB bios password
I have Dell Inspiron 14-3552
Service tag _ GHNGYB2
Hard drive s/n._ WBYOPW8X
I forget my hard-drive bios password.how can i unlock it.
Can you PLS HELP iv a dell inspiron 1545 laptop im a beginer i need sum extra advice dell want a big payment coz its 2nd but its coz im learning
how can i get the.master password fir HP laptop?
what is the website ? Its help for me . I want my BIOS password for acer laptop .
I ca’nt enter my laptop setups coz its asking for a password, so please help coS i cant even load a Windows, when i enter F2 for setup it needs password, how can i resets it please help(acer) motherboard
Dell d810
Plz give mi the bio password Lenovo i3 version
acer travelmeate bios password (06829)
i need acer iconia w701 bios password
i have a toshiba sitellite board password ones you on it the password will come on pleas i ned a solotion thanks
I have a emachine – windows 7 – I have never used my computer – I bought it 2 years ago and my husband was killed in a trajic accident – I ahd placed my password in at the time and cannot remember it – can anyone tell me how to get it, reset it or get around it in easy terms – I am not the smartest computer person and am having trouble with all the ways I have been told.
your not believable
I like your application!
how toopen SATA HDD password
please help me with information on how to remove a HDD password on a dell vostro 1510
Hdd unlock wizard setup, this is the software download try it
How do you recover the password using only the laptop serial number
please give solution my hand phone unlocked leonovo a60
I have a asus 1215b please help with a bios password
How to Clear Your Computer’s CMOS to Reset BIOS Settings?
Need help . Forgot bios password. Need to erase it or reset it.
Lenovo G580
Bios password
i Am Try All option but not remove bios password please help me
If the following 2 methods, especially the battery removal method (the small round battery as shown in the photo, not the big removable battery in laptops) does not work, you may have to refer to your manufacturer.
I have a asus laptop and the model number is D550MAV-DB01 and I need the bios password
My daughter accidentally keyed in wrong password to her ASUS A43S laptop, now the laptop request for BIOS password which I can’t remember. Can anybody help me on how to recover the BIOS password.
Have you tried removing the laptop battery? the tiny battery inside the laptop? removing the round tiny battery for a few minutes will reset your BIOS with no password. Remember, your warranty voids if you open your laptop. And if you have important data, make sure the person that handles your laptop perform the task in front of you.
Thanks Ngan, I have tried it. It doesn’t work. Where can I buy the master password for this Asus A43S.
I don’t think you can ‘buy’, you’ll have to send to Asus service center. Perhaps they have a ‘master key’
i know my bious password bt now i want to remove it …. bt i can’t so what can i do ?
in your BIOS settings, choose to remove or reset the BIOS password. When given a choice, leave the password field empty and save. this will remove the bios password
Hello I need help .. i forgot my acer aspire one d257-13448 netbook bios password. No error code
after 3 unsuccessful attempts. Plz help me reset bios password? email:bartdman888@gmail.com
Please, any recommendation for Aspire V3-772G. Is it possible to recove or clean Admin password? I use uset password daily bot forgot this one. Please, help…
Got a Dell inspirion mini 1018 hdd password comes on right when i turn it on can’t get past it says hdd password 03465 service tag 53bqxni help please
I forgot Asus bios password on my Asus eee pc 1000hd. Does anyone know master password. I haven’t used my netbook for about 4 years now. Thank You
I need dell latitude E6430 bios password removal
My asus laptop is asking for bios password after my daughter was playing with it. Can you help?
Laptop model is asus x551m.
Thanks!!!
If you have a recent Dell laptop, the only cure is to find someone to install a new BIOS chip, or have Dell replace the motherboard if it is under warranty. Just went through this with a client who has a 2 year old +- Dell Inspiron 3542, and that is the Gospel from Dell Tech support. No jumpers on the mobo, no magical master password from Dell. Dell removed the jumper from their laptops in 2004, but the encryption has gotten stronger and stronger to the point where it would take the NSA to crack it, because even Dell has a very low success rate. We never got to the point of discussing if those fixes would help if the PW was also set on the hard drive, but I suspect that in that case, you are totally SOL. If you do set either of those passwords, for your own sake do regular backups of your important files to an external drive.
Not exactly… try booting a burnt iso of this collection of hack gems : “Hiren’s Boot CD”
Do you need BIOS Password then read more this article
I need bios password for lenovo G50-30
I have hp elitebook 8460p and I have forgotten my bios password I also try to remove cmos battery but it does not worked
hi I have Packard Bell easy note laptop with Toshiba hard drive..plz help it required HDD password please
Yes but how???
How can I get advent bios password
Please I need bios pheonix password. I will try show me
3535<
I have a ASUS windows 8,Model:X200M notebook PC.I forgot the power-on password and can’t use the machine.The notebook doesn’t have CD rom/DVD drive.On top of that my battery may have gone as iam only using 240V ac power.
Would appreciate,if someone can help me on this issue
Anyone plz give master password for dell i forget bios password i am in trouble help me
Hi I forgot my bios password on my techno winpad 10 pc- tablet how can get it unlocked. It appears on the screen error status and won’t come on unless i put the password which I forgot. Thanks.
Hi how to resets Bios for – Dell Vostro all in one.
Please do assists.
Thanks.
Iam handicap an i need a bios password for a dell latitude E4310 i cant physically do it
Use software to recover.
https://bios-pw.org/ – pass bios reset – work
04 – Overload The Keyboard Buffer – while pressing ESC (eye 120 times with the other hand, press Enter) works on older computers.
Тhanks
My Acer Extensa 2519 is driving me crazy. Removing the battery for the whole night was not helping. There is a reset button, but pressing it for 30 seconds still doesn’t reset the password. All manuals I find online are about batteries or jumpers, but this one has two little buttons and the thing with the battery doesn’t work. :(
Pls my brother I need to know how to remove bios password for HP elitebokk 8460pans 8470p thanks
Great site. The video for removing bios is clear and without external nonsense.
how to reset bios thomson neo 14-2 32bs ?? plz help
My Asus system is asking for bios password. Please how do I bypass it.
my laptop is toshiba portege R-830-S8320
when i turn on the screen is black and on the screen is passord=
so may you help me plz
plase i need a pasword bios for dell inspiron n 5110
please i need a password bios for dell inspiron 14 3000 series
After 3 attempts my laptop will get off.
but my system tag is showing while i on the laptop
WHICH ONE WILL WORK ON A ASUS LAPTOP
Hmm, I need a key generator for Insyde H20 BIOS – 10 digits code, not 8 digits…
I have ASUS, ACER & SONY VIO any model laptop BIOS Password solution.
hi please can help me i have a acer swift 3 and it has a 10 digit key for recovering password
Guys pls help Acer aspire ES1-533 need current password even if I press f2 pls help help guy’s then then it says no bootable device found after
My laptop (Y11C) is asking for BIOS password.
Anyone have solution kindly tell me.
Thanks
Hey! PC CMOS Cleaner is an easy-to-use tool to recover, delete, decode and display the superior passwords stored in BIOS whatever the brand is.
Need bios password master key for Dell inspiron 3521
lenovo password reset please
How do you bypass the hdd/sdd bios password I cant seem to get rid of it off my Toshiba laptop
Password for Lenovo Thinkpad x270
service tag: DF40FR1
Hard-drive S/N: A91P0369
i lost my hdd password bcs i set it many yrs ago, but now i forgot, im working with my laptop pz help me out… ty
debug o70 2E o71 FF quit
say me pls, how to type debug on command promt.. because when I type it its show me as : debug is not recognized as an internal or external command, operable program or batch file.
send me a screenshot of typed dos promt…
I have a Thinkpad T470s itel i5 7th gen. It was bit locked. I changed some of the boot order and there was No passwords set. I’ve since lost my usb stick and back up of the bios settings.
When I power up the thinkpad asks for pop password or svp?
The fn key Esc and Fn giggle on and of but the f1 only giggles to red led on of.
I did also change the graphics down thunderbolt charge.
Any help please. Im scared to take it apart.
Hi, Only my Camera on my lap top is password protected in the BIOS.
Now that I have to work from home, I need the camera for tele conferences.
I have forgotten the password.
I did this to protect my children when using my laptop.
It is a Dell
My question is – can i use any one of the suggestions above to remove the password?
i need BISS lenovo Thinkpad T400
I have an asus laptop with a broken screen and I’m locked out of the computer because the master password was reset and it doesn’t accept the new password so it is locked down I can’t get into it any suggestions ?
Can anybody help to solve this. How to bypass power on password on lenovo pc
I tried two methods already
1. Removing cmos battery
2. Booting using pen drive which contain OS
Nothing worked
i need password for hp probook g5 645
Password for toshiba
Hello!!! Please I need the password for dell latitude 5410 with the serial number 71KG163BFC8
pppppaan
* for some Dell codes press Ctrl-Enter, not Enter, when entering code into the BIOS
Hello everyone,
i have a lenovo ideapad 330 which i forgot the password for the bios, please help me reset the bios for.
Samsung notebook NC110
Help with bios password recovery please.
My screen is dark blue with a light blue rectangle that says “invalid password
hello, I have an ASUS EXPERTBOOK B1500CEAE model computer and there is bios version 304 on it. I forgot the bios password and I can’t figure it out. Can you help please?
I tried removing the bios battery, the result is unsuccessful.
Bios password for Lenovo
Is is possible for Connex laptop?