How to password protect and encrypt the files in their portable Flash Drive, USB Hard Disk and USB SSD? This is to prevent it from falling into the wrong hands in the event you lose it, it may or may not contain personal data, given that there is nothing to lose, why not password and encrypt it? Even if you leave it on your table, it can be stolen by someone and returned to the original place with the information accessed without you knowing it. This is why it is important to password lock and encrypt your portable USB devices.
Continue ➤ 4 Free Full Hard Disk 256-bit AES Encryption Key For Data, File And Email
Before they begin, it is important to know that there are 2 types of encryption for portable USB Flash Drive / HDD and SSD – hardware encryption and software encryption. The list in this article are portable software based encryption for your USB Flash Drive, if you are using Windows Vista and Windows 7: Enterprise and Ultimate editions, Windows 8 and 8.1: Pro and Enterprise editions, Windows 10: Pro, Enterprise, and Education editions, Windows Server 2008 and later, use BitLocker.
BitLocker is a full disk encryption feature included with Windows Vista and later. It is designed to protect data by providing encryption for entire volumes. By default it uses the AES encryption algorithm in cipher block chaining (CBC) or XTS mode with a 128-bit or 256-bit key. CBC is not used over the whole disk; it is applied to each individual sector.
Hardware Encryption VS. Software Encryption
Software encryption options are available on the market as a cheaper alternative to hardware encryption, but the disadvantages tend to outweigh the benefits. It often requires numerous updates to keep up with hacking techniques, could be quite slow, and may require complex driver and software installations.
Software encryption also may not provide the full security that businesses are expecting, to keep sensitive information from falling into the wrong hands. Though software encryption is better than having no encryption at all, it may still be vulnerable to user error, leaving data to fall through the cracks and be susceptible to potential thieves.
Since software encryption requires users to follow certain procedures in order to secure the data, users may forget – or choose to ignore certain aspects of the encryption process.
With hardware encryption on secure USB drives, the AES encryption process is handled automatically, built right in with a small chip inside the drive itself. Once original data is encrypted, it becomes undecipherable in the background and is locked away under encrypted storage within the drive.
If a thief were to try to gain access to the data without the password, the attempt is by all practical means impossible. But once the user enters their private password, the data is decrypted instantly, and made fully available to the user.
Hardware-Based Encryption:
- Uses a dedicated processor physically located on the encrypted drive
- Processor contains a random number generator to generate an encryption key, which the user’s password will unlock
- Increased performance by off-loading encryption from the host system
- Safeguard keys and critical security parameters within crypto-hardware
- Authentication takes place on the hardware
- Cost-effective in medium and larger application environments, easily scalable
- Encryption is tied to a specific device, so encryption is “always on”
- Does not require any type of driver installation or software installation on host PC
- Protects against the most common attacks, such as cold boot attacks, malicious code, brute force attack
Software-Based Encryption:
- Shares computers resources to encrypt data with other programs on the computer – Only as safe as your computer
- Uses the user’s password as the encryption key that scrambles data
- Can require software updates
- Susceptible to brute force attack, computer tries to limit the number of decryption attempts but hackers can access the computer’s memory and reset the attempt counter
- Cost-effective in small application environments
- Can be implemented on all types of media
Hardware based encryption is always the better option, all the drives in this roundup use the 256-bit AES hardware encryption required to achieve FIPS 140-2 Level 2 certification. SanDisk SecureAccess did not make it to the list because it is a software based encryption. Below are 3 hardware based encryption available worldwide.
- Kingston DataTraveler and IronKey series
- Corsair Flash Padlock
- Verbatim Corporate Secure USB Flash Drive
1. Rohos Mini Drive
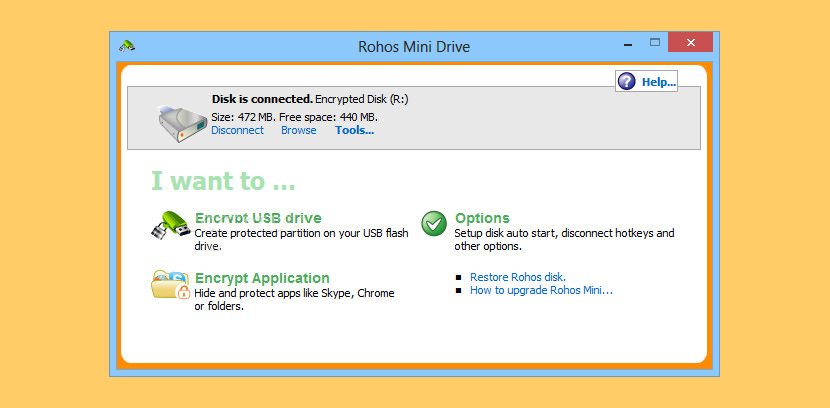
Rohos Mini Drive password-protects a USB flash drive by creating a hidden and encrypted partition on the disk. If you have many private files on the USB drive and want to keep them secret, you can protect them with a password and strong encryption using Rohos Mini Drive. It also offers a portable encryption tool for working with an encrypted partition on any PC.
With portable Rohos Disk Browser you can work with a password-protected partition on any PC without Administrator privileges or installing additional software. It works like Windows Explorer, displaying folders and files. This portable utility is handy when you don’t have access to your computer or laptop.
- You can access your secret volume by entering the correct password.
- On-The-Fly AES 256 bit key length encryption without Administrative privileges.
- File Virtualization – prevents secret data from leaking outside an encrypted disk in temporary file folders, the Registry, the Recent Documents list, etc.
- Secured virtual keyboard – protect an encrypted disk password from a keylogger.
2. USB Flash Security
Free (Max 4GB Drive)
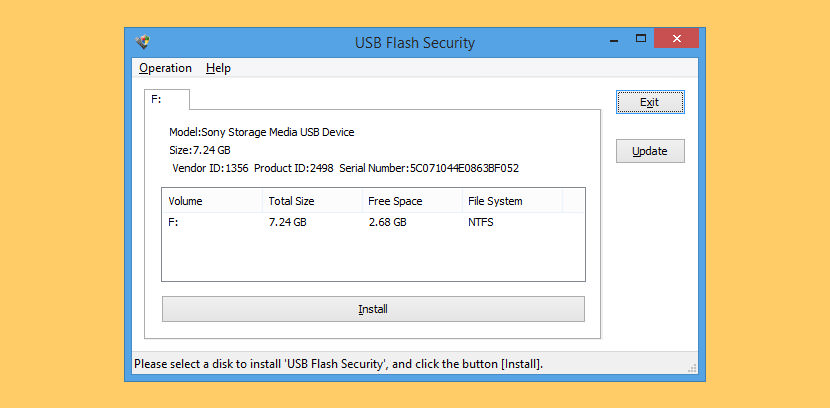
Lost or stolen mobile devices are a growing data security threat, yet there’s no need to panic over sensitive data falling into the wrong hands if it’s protected. That’s where USB Flash Security from Kashu System Design comes in. It’s a free USB security utility for mobile devices.
USB Flash Security’s compact, tabbed interface displays all installed disk drives on your PC, but the software will only install on those drives with USB access. It’s a keep-it-simple layout: there’s a display window, file menus for Operations and Help, Exit and Update buttons, and the Install command bar, but that’s it. They inserted a USB flash drive, and USB Flash Security immediately identified it.
- Software is installed onto USB Flash Drive, works on any computer without “USB Flash Security”.
- Comes with AES encryption.
3. Cryptainer LE Mobile
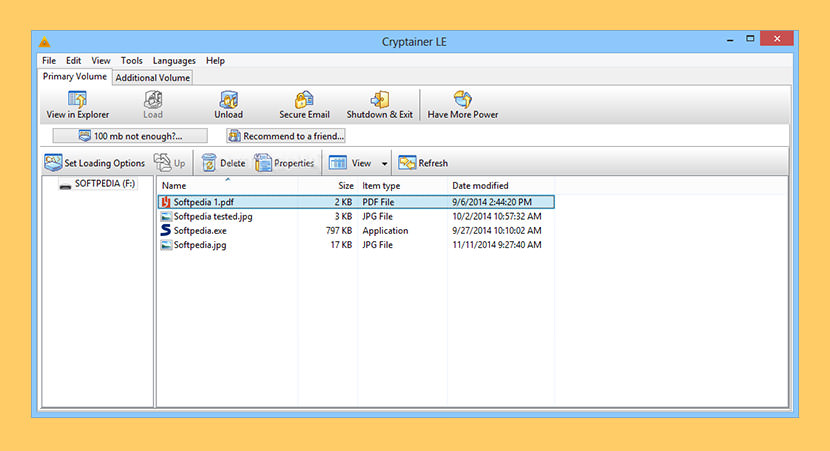
You will find the mobile feature of Cryptainer very useful. Cryptainer can be installed directly on a USB / removable drive as a “stand alone” install. One can carry this installation of Cryptainer (‘Cryptainer Mobile’) to different machines without having to install Cryptainer on the host machine. Sensitive data can be stored within an encrypted volume file that can only be accessed through Cryptainer, with the correct password.
- Cryptainer LE free encryption software is a comprehensive solution to encrypt any data, any disk, drive, file, folder on Any Windows PC. It has a very Simple, Easy-to-use interface to encrypt and decrypt files on the fly. It allows you total privacy and security without changing the way you work.
- Cryptainer LE creates an unlimited number of encrypted drives on your hard disk that appear as Real Drives in Windows. It functions like any other regular drive on your computer.
- Fast Encryption – Cryptainer LE is fast. You will barely notice the difference in speed as compared to a regular “Copy Paste” function.
- Storage Flexibility – Cryptainer LE allows the creation of encrypted disk drives on removable media. This allows for the flexibility to store and port data on removable media like Zip disks, tape drives, external drives (Flash Disks, USB drives, pen drives). It also allows users to Password Protect Folders, Files on CD ROMs, DVD’s.
4. VeraCrypt Portable
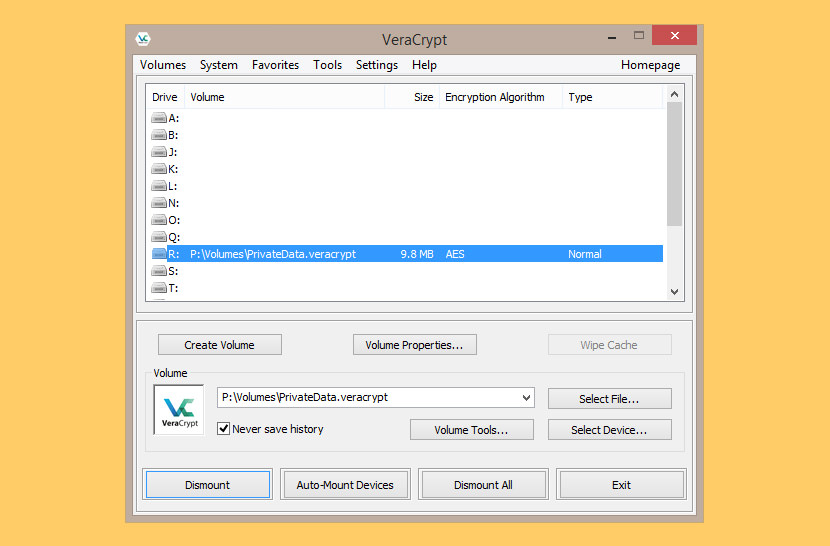
VeraCrypt is a free disk encryption utility allowing you to both encrypt full physical drives and make encrypted logical volumes. VeraCrypt requires admin rights to operate. VeraCrypt is a free disk encryption software based on TrueCrypt 7.1a. It allows secure encryption of full disks as well as virtual volumes that can be mounted on the fly. VeraCrypt has support for various encryption algorithms (AES, Serpent, TwoFish), keyfiles, security tokens, hotkeys, and more.
Encryption Algorithms, VeraCrypt volumes can be encrypted using the following algorithms: AES, Camellia (Mitsubishi Electric and NTT of Japan), Kuznyechik (National Standard of Russian Federation), Serpent, Twofish, AES-Twofish, AES-Twofish-Serpent, Serprent-AES, Serpent-Twofish-AES, Twofish-Serpent.
5. LaCie Private-Public
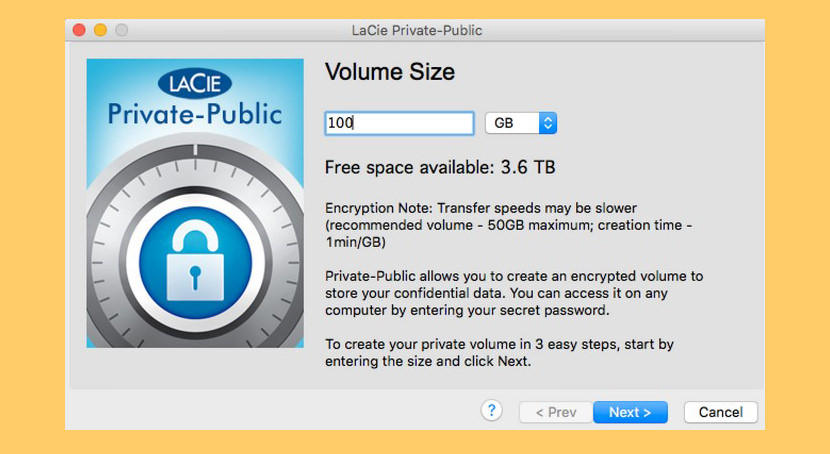
LaCie Private-Public is the easiest way to protect your important and confidential files. LaCie Private-Public is a standalone application that uses state-of-the-art encryption technology. Sitting on your LaCie USB Key or any other mobile drive, it doesn’t need to be installed on a computer to run. Whether you’re away from home on a PC or Mac computer, simply plug in your key, launch LaCie Private-Public, and enter your password to gain access to all your files.
Protect your office documents, personal photos, passwords, and other confidential information. With one- click encrypt/decrypt capabilities, LaCie Private-Public is probably the easiest most usable and most secure encryption software you will find. LaCie Private-Public is the perfect companion to any LaCie mobile device or USB key.
6. CipherShed
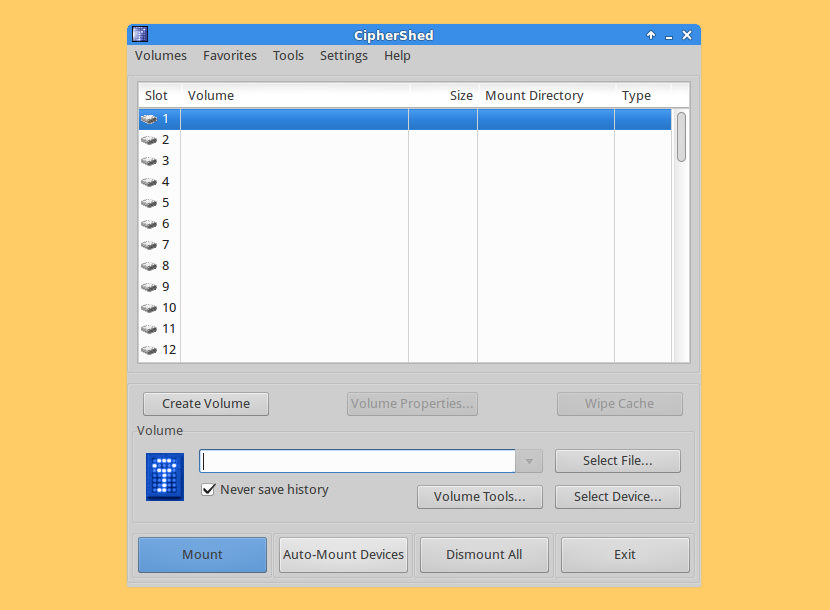
CipherShed is free (as in free-of-charge and free-speech) encryption software for keeping your data secure and private. It started as a fork of the now-discontinued TrueCrypt Project. Learn more about how CipherShed works and the project behind it. CipherShed is cross-platform; It is available for Windows, macOS and GNU/Linux. Although packages for OS X and Linux do not exist, yet, users of those platforms will need to compile CipherShed.
7. USB Secure
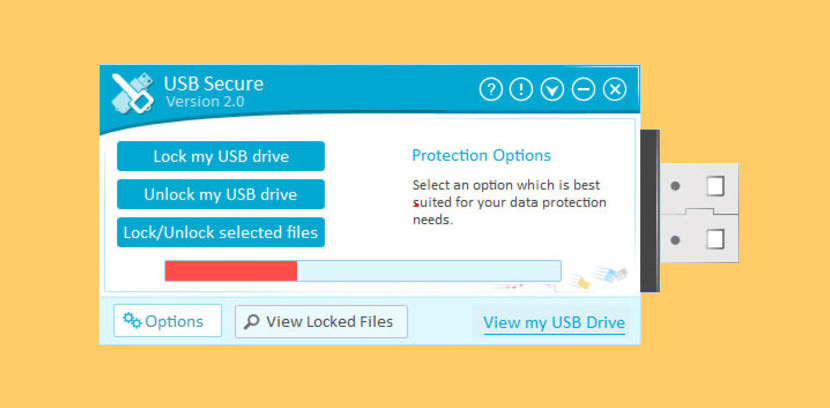
[ Not Free ] Passwords protect your USB, SSD & external drives with reliable security for your files & folders on USB Drives. USB Secure lets you password protect your USB drives, SSD drives, external drives and memory cards. Protection is PC independent and does not require installation or administrative rights on the other end. You can unprotect your data by entering the password again. Works in all flavors of Windows.
- Portable Security – Compatible with all portable drives such as thumb drives, memory sticks & external hard-drives.
- Plug and Play – PC independent, does not require installation on the other end, true plug and play protection.
- One Click Protection – With a single click, your files & folders are locked using the latest technology in data security.
- Anti Theft – Multiple layers of security prevent criminals from accessing your receptive files and folders.
- Virtual Drive – View or modify your protected files & folders securely through the virtual drive interface.
- Fast and Easy – Simple & user-friendly interface makes it effortless for anyone to quickly lock their files & folders.
- Compatibility – Works on all versions of Windows, for example Windows 2000/ XP/ Vista / 7 / 8
- Reliability – Patent pending protection methods ensures your data will remain secure under all circumstances.
8. EncryptStick
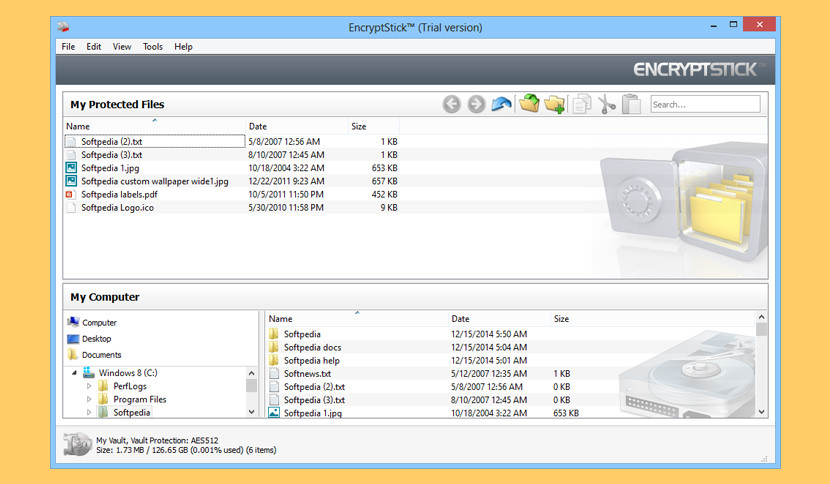
[ Not Free ] Everyone has private information and files on a computer, laptop, flash drive, or some other portable storage device that should have extra security. Whether these files are photos, videos, financial records, banking information or other sensitive data, they are vulnerable to damage, loss and even theft.
Loss and misuse of private information can have serious consequences: embarrassment, expense, even job loss, are all possible outcomes, particularly when important information falls into the wrong hands. EncryptStick can quickly, easily and permanently secure your important information and protect your privacy.
- Runs on Your Computer and Any USB Flash Drive – EncryptStick runs on PC, Mac and Linux computers and all recently made USB flash drives. EncryptStick software installs quickly and easily. When installed on a flash drive, you can use EncryptStick on any PC or Mac anywhere in the world.
- Encrypt & Decrypt Your Private Files – EncryptStick turns your flash drive into a highly secure, private vault where you store the files you want to protect: photos, music, videos, documents, in all file types. You can create “vaults” for encrypting and protecting files on most writable media including Mac, PC and Linux platforms, shared network drives, external hard drives and additional USB flash drives. More media storage options to come. EncryptStick dynamically sizes vaults so that each only takes up the space it needs to store your protected files. Vault contents are only visible to you and remain hidden to others, unless they have your EncryptStick enabled flash drive and your password.
- Strong & Fast Encryption – The EncryptStick encryption engine uses fast and strong AES algorithms. You have the option to encrypt your vaults with 128, 256, or 512-bit AES ciphers. Their encryption is registered and government approved, and is FIPS 140-2 compliant. In an upcoming release, they will offer a 1024-bit encryption option.
- Limited Login Attempts – Stop brute force hacking, ten failed login attempts locks EncryptStick’s login screen for a full minute thereby significantly reducing susceptibility to brute force password attacks.
9. USBCrypt
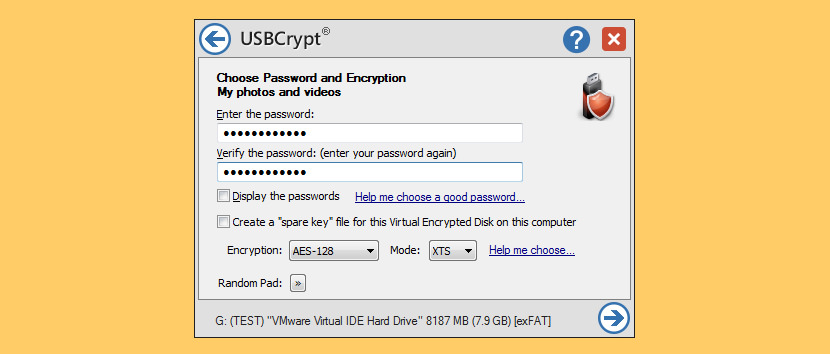
[ Not Free ] USBCrypt is a powerful software encryption utility for Windows 10, 8, 7, Vista, XP that protects your sensitive information from unauthorized access. It locks the bad guys out, and protects your personal, business, and financial data. Use USBCrypt to encrypt your USB and other removable and fixed drives with strong encryption. USBCrypt uses the industry standard AES encryption algorithm to protect your files, the strongest protection available.
- From 1MB to 128TB (which is the current limit of Windows), USBCrypt can encrypt drives of any size. After the initial encryption, the large drives work just as fast as the small ones.
- From Windows XP to Windows 10, both 32- and 64-bit, with the latest service packs and hotfixes, all are supported by USBCrypt.
- USBCrypt uses the industry-standard AES encryption, which makes it impossible for anyone to get to your files without knowing the correct password. There is currently no technology available to anyone in the world to break AES encryption.
10. GiliSoft USB Encryption
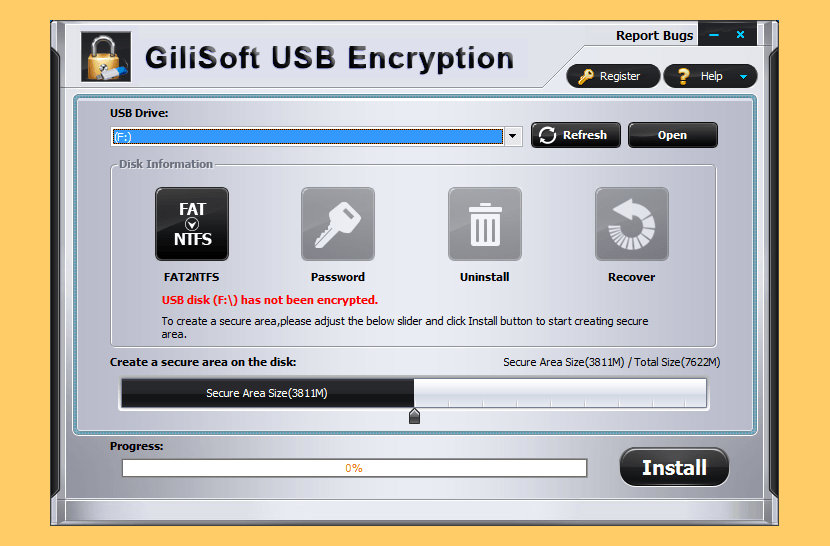
[ Not Free ] The USB flash disks of today are a very efficient and excellent solution for file sharing, carrying around or even backup. But USB Flash drives are designed to be small in terms of size, it is also easy to misplace or worst case, get stolen. GiliSoft USB Encryption enables you to encrypt a USB flash drive, all these problems can be handled with ease.
GiliSoft USB Encryption is a comprehensive, easy-to-use solution for USB security that supports encrypting portable storage devices (external drive) and can divide external drive into two parts after encryption: the secure area and public area. Converts a regular USB flash drive into a secured one in less than a minute, data on the protected area (Secure area) is encrypted by 256-bit AES on-the-fly encryption.
11. USB Security
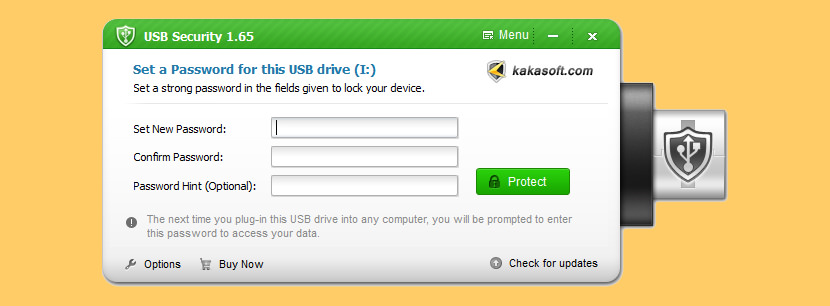
[ Not Free ] Kakasoft USB Security well protects your sensitive information in USB drives with the strongest encryption technique. This USB disk security program ensures comprehensive data security of your confidential data on your USB flash drives and protects them from unauthorized access with the adoption of marvelous cryptography and advanced encryption method.
Sensitive and valuable data needs urgent protection. With feature-rich USB Security you are able to secure the external drive as a whole and supports password protecting USB flash drive, HDD hard drive, thumb drive, pen drive, memory stick, memory card and all other portable storage devices in Windows systems. You will never need to worry about leakage or breach of any valuable information even if you lost the USB disk.
12. USB Locker
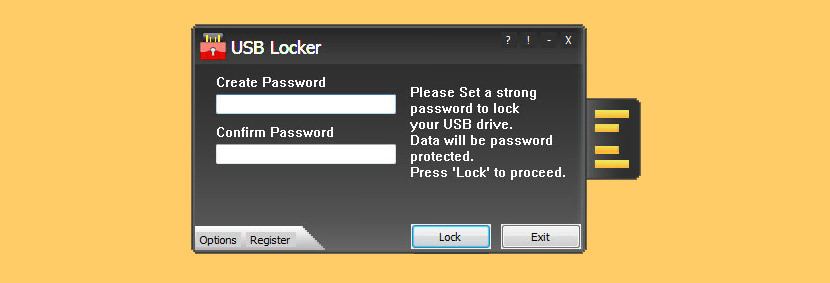
[ Discontinued ] USB Locker is a strong portable drive protection application for all kinds of USB drives including flash drives, thumb drives, memory- cards and external drives. USB Locker offers you unparalleled protection across multiple- platforms including Mac, Windows and Linux.
Keeping at a complete mind rest, USB Locker gives your data a robust protection against unauthorized access and keeps your data safe from misuse.
13. Kruptos 2 Go
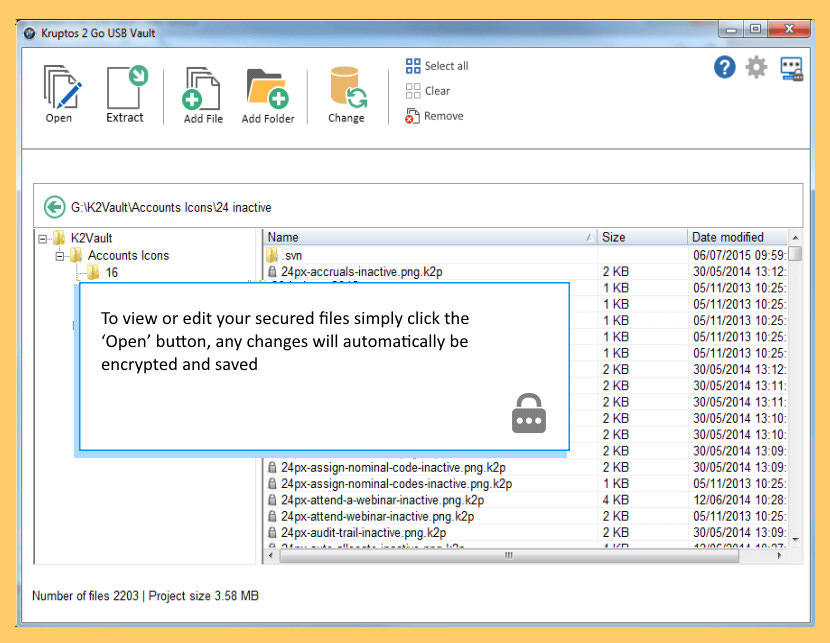
[ Discontinued ] USB drives are the most common way to move data from one computer to another. They are small, portable and often contain highly sensitive data which can be worth millions of dollars. USB drives pose a security risk and can be easily lost, stolen or misplaced.
Kruptos 2 Go is a password protection tool for your USB Drive which protects your privacy and important data from data theft, data loss or leaks. Just drag and drop your files and folders into Kruptos 2 Go’s encrypted ‘Vault’ and they will immediately be password protected which prevents your important data from being modified, read or even accessed without the correct password.






Rohos Mini Drive has a keylogger, as reported by Zemana antivirus,
which is as good as hitman pro. and is highly rated. Jun 2017
Good day, Try NYSMNYD(now you see me now you don’t) to password protect your folders, fast and easy to use, its portable and its freeware. you can download it at aeontime.blogspot.com
Hello Mitchelle,
Mitchelle, automatic random password creation is a very dangerous feature for a data protection program to have because the possibility of someone accidentally locking their files using a random and unknown password is very high.
It happened to me while testing your program, but fortunately the folder did not contain any important data.
Thanks for your program but unfortunately, due to the aforementioned pitfall, I can neither use nor recommend it to anyone
With kind regards
Tech Nut
Good day, Tech Nut, automatic password is the default option, you can copy it elsewhere or take screen shot using your cellphone but you can change it with your favorite password if you like. Different folders can use different password so different user can use single USB disk. Hope you try to use it again.
Yours truly
Mitchelle
Kindly recommend a cross-platform (MAC, Windows) software that provides simple password-protection (not encryption) on external portable drives (HDD/SDD). From a user experience perspective, once the password-protection is activated on a portable drive on a MAC (or WINDOWS), than he/she would simply plug the drive on another laptop (MAC or WINDOWS), enter the password when prompted and read/write to the drive.
Any suggestions would be most helpful. Thanks!
Kakasoft USB Security does not encrypt it just hides your stuff.
Its all accessible using freeware tools.